How-To
Windows Sandbox, Part 2: How To Install and Use the New Windows 10 Feature
In this second article of a two-part series, Tom Fenton takes you step-by-step to create a temporary desktop environment with Windows Sandbox.
Due to the length of this article on Windows Sandbox, I broke it up into two parts; in the first part I explained how I installed a Windows 10 version that can run Sandbox, and in this part I focus on how I installed and used Sandbox.
Turning on the Windows Sandbox Feature
Sandbox is a feature of Windows 10, so I didn't need to download anything else -- I only needed to enable the feature in Windows.
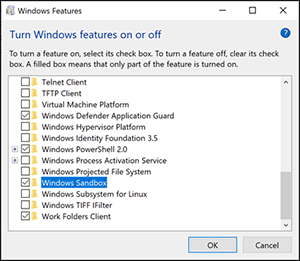
Once I verified that my system met the requirements for Sandbox, and I installed the beta build of Windows, I brought up Control Panel, selected Programs and then Turn Windows Features On or Off. From this dialog, I selected the Windows Sandbox checkbox and then clicked OK (Figure 1). I was then prompted to restart my laptop.
 [Click on image for larger view.]
Figure 1. Turning on Windows Sandbox in the Windows features dialog box.
[Click on image for larger view.]
Figure 1. Turning on Windows Sandbox in the Windows features dialog box.
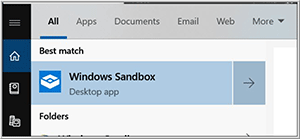
Once my system was restarted, I logged back in to it, entered Sandbox in the Windows search bar, and then clicked the Windows Sandbox app icon when it appeared (Figure 2).
 [Click on image for larger view.]
Figure 2. Starting Windows Sandbox.
[Click on image for larger view.]
Figure 2. Starting Windows Sandbox.
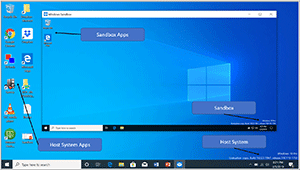
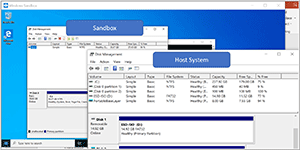
After a short wait, I saw a Sandbox icon on my Windows desktop. As this is a "fresh" version of Windows, none of the apps or settings from my host Windows installation were present on it (Figure 3).
Using Sandbox
As I used Sandbox, I did find some peculiarities with it, such as being able to copy and paste files into the Sandbox from my base Windows, but not being able to drag and drop files to the Sandbox. You should also be aware that if you cut and paste files into the Sandbox from your host system, rather than copy them, they'll be permanently deleted when you remove the Sandbox.
 [Click on image for larger view.]
Figure 3. Opening the Sandbox icon shows no apps from my host system are included.
[Click on image for larger view.]
Figure 3. Opening the Sandbox icon shows no apps from my host system are included.
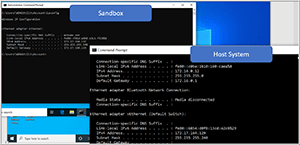
I could use applications, such as Web browsers, ping, and nslookup, that used the network without any issues from the Sandbox, and when I looked at the network setting in my Sandbox system it had a different IP address than my host Windows system (Figure 4). When I tried to connect an RDP session into my Sandbox from my host system it failed; I didn't investigate whether this was a feature of Sandbox or just a configuration error on my part.
 [Click on image for larger view.]
Figure 4. Different IP addresses for the Sandbox and host sytem.
[Click on image for larger view.]
Figure 4. Different IP addresses for the Sandbox and host sytem.
By reviewing the disk drives on my Sandbox system, I found that it had a much smaller disk drive than the base Windows system (Figure 5).
 [Click on image for larger view.]
Figure 5. The different disk drive sizes of Sandbox and the host system.
[Click on image for larger view.]
Figure 5. The different disk drive sizes of Sandbox and the host system.
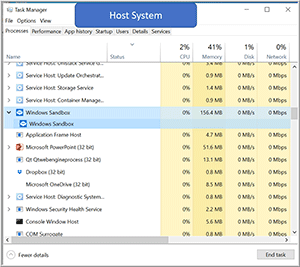
I looked at the Task Manager on my host system and noticed that the Sandbox system was using very few resources (Figure 6).
 [Click on image for larger view.]
Figure 6. The host Task Manager.
[Click on image for larger view.]
Figure 6. The host Task Manager.
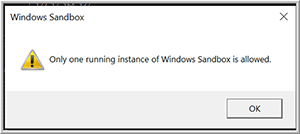
When I tried to bring up a second instance of Sandbox, it failed with a message stating that "Only one running instance of Windows Sandbox is allowed" (Figure 7).
 [Click on image for larger view.]
Figure 7. A second Sandbox instance cannot run.
[Click on image for larger view.]
Figure 7. A second Sandbox instance cannot run.
To further test Sandbox, I downloaded and installed Notepad ++ and Wireshark on it, and both applications ran without any issues.
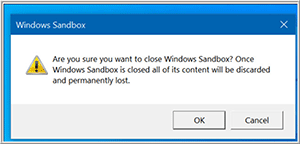
Once I was finished with my Sandbox system, I simply closed it by clicking the X in the upper-right corner of the Sandbox app and then clicking OK to confirm that I understood that all content I had in the Sandbox would be deleted after closing the app (Figure 8).
 [Click on image for larger view.]
Figure 8. Closing Sandbox.
[Click on image for larger view.]
Figure 8. Closing Sandbox.
Deep Dive into Windows Sandbox Technology
To get a better understanding of the technology behind Sandbox, I took a look at the information that Microsoft had published on the feature, and in doing so I discovered that Microsoft uses its Windows Container technology to provide the sandboxing functionality. Windows Containers were "designed to run in the cloud," and it looks like Microsoft integrated this technology with Windows 10 and modified it so that it would work fine on laptop and desktop devices running Windows 10.
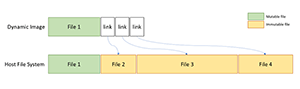
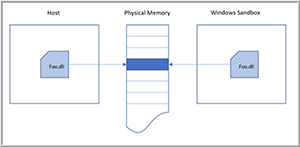
Microsoft has a write-up that includes a couple diagrams on how Sandbox works. Figure 9 shows that the Sandbox (dynamic image) will use a link to files on the host Windows system and will only create separate files when the data in the Sandbox has changed. Figure 10 shows that the Sandbox will use the same real memory as the host Windows system. The article goes on to explain how Microsoft has wrapped other measures around these techniques to ensure proper security for the host system from the Sandbox.
 [Click on image for larger view.]
Figure 9. Sandbox disk writes. [Source: Microsoft]
[Click on image for larger view.]
Figure 9. Sandbox disk writes. [Source: Microsoft]
 [Click on image for larger view.]
Figure 10. Sandbox memory [Source: Microsoft]
[Click on image for larger view.]
Figure 10. Sandbox memory [Source: Microsoft]
Microsoft also mentions how the company created a new scheduler policy that gives high-priority host processes the right to preempt less important tasks in the Sandbox to ensure that the host responsiveness will not suffer because of the Sandbox.
Using Windows Sandbox on vSphere
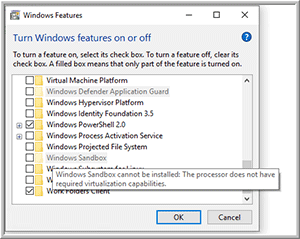
After many attempts, I could not get a Windows 10 virtual machine (VM) running on vSphere 6.7 to successfully run Sandbox. When I first tried to enable Sandbox, it was grayed out and if I hovered over the feature it said "Windows Sandbox cannot be installed: The processor does not have the required virtualization capabilities" (Figure 11).
 [Click on image for larger view.]
Figure 11. Virtualization capabilities are missing.
[Click on image for larger view.]
Figure 11. Virtualization capabilities are missing.
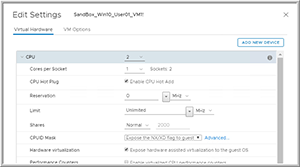
To try and get it to work, I shut down my VM, went to my vSphere Client, and selected the Expose hardware assisted virtualization to the guest OS option for the system (Figure 12).
 [Click on image for larger view.]
Figure 12. Exposing the hardware virtualization settings.
[Click on image for larger view.]
Figure 12. Exposing the hardware virtualization settings.
After exposing hardware virtualization, I could then enable the Sandbox feature and even start it; however, after a few minutes I received an error message that "Windows Sandbox failed to start" (Figure 13).
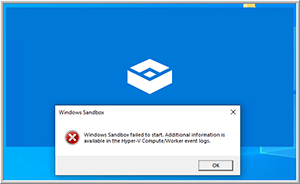 [Click on image for larger view.]
Figure 13. Sandbox failed to start.
[Click on image for larger view.]
Figure 13. Sandbox failed to start.
It's possible that my VM could've been further tweaked to allow the Sandbox to run, but as my laptop was able to run Sandbox, I didn't pursue other avenues to get it run in on a VM.
Wrapping Up
Although it did take me a while to find and install a version of Windows that had the Sandbox feature, I didn't have any issues during the brief time that I worked with it; I was able to install and run applications in the Sandbox, and when I stopped my Sandbox session it cleaned up all traces of the applications. Even though the only use case that Microsoft has laid out for Sandboxes is application testing, the technology may lend itself to some other interesting use cases, especially if the company allows more than one instance of it to run at a time and also allows RDP sessions to connect into it.
About the Author
Tom Fenton has a wealth of hands-on IT experience gained over the past 30 years in a variety of technologies, with the past 20 years focusing on virtualization and storage. He previously worked as a Technical Marketing Manager for ControlUp. He also previously worked at VMware in Staff and Senior level positions. He has also worked as a Senior Validation Engineer with The Taneja Group, where he headed the Validation Service Lab and was instrumental in starting up its vSphere Virtual Volumes practice. He's on X @vDoppler.