How-To
What Is a Modern Desktop?
Paul Schnackenburg takes a look at just what a "modern desktop" means today in the Microsoft IT camp -- investigating different management approaches that just might improve the lives of you and your end users.
Whenever you hear Microsoft talk about end user computing it's always Modern Workplace and Modern Desktop. There's even a certification exam for it, Managing Modern Desktops.
It's always a bit dangerous naming something modern or new, because as time passes it's no longer modern. Take the NTFS file system, now well over 20 years old with the actual name of New Technology File System -- not so new anymore. In fact it's being replaced by the Resilient File System (RFS). Anyway, this article is going to clarify what's meant by modern desktop, what technologies apply and why you would want to move your business to this paradigm.
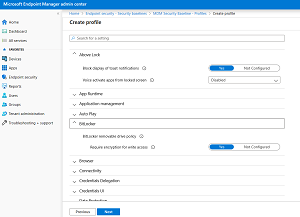 [Click on image for larger view.] Endpoint Manager Security Policy
[Click on image for larger view.] Endpoint Manager Security Policy
The Not-So-Modern Desktop
Traditional IT approaches to managing fleets of Windows desktop and laptops are built around imaging. You order new devices from your favorite OEM. When they arrive, they're connected to the network, and the Standard Operating Environment (SOE) replaces the version of Windows on the PCs with an in-house-created golden image. This image is hand-crafted with just the right drivers and applications, along with configurations that the business requires. If you have sufficiently differing hardware platforms, you'll need a different image for that brand or model of desktops and laptops. As the images multiply, so does the work of keeping them up to date with patches (monthly) and application updates, especially if you opt for thick images with a lot of applications already installed in them. A thin image only has the OS and a few applications that every user should have access to.
Once the PCs are deployed, you'll need a system (like System Center Configuration Manager, now called Endpoint Manager) to deploy additional applications and patches. To ensure that the configuration stays secure and manageable you use Active Directory Group Policies (GPOs) to push out an array of thousands of settings. Oftentimes these PCs are locked down tight (following the "Stalin school of IT management") hindering users in their daily work (but at least it's secure!).
This is how it's been done for 25+ years -- why change it now? Well, all this manual labor is time-intensive and thus costly, and it also only works for corporate-issued devices but not Bring Your Own Devices (BYOD, sometimes known as Bring Your Own Disaster). Furthermore, it's very centralized, devices must be set up in the IT department and it's hard to manage branch office deployments.
Modern Desktop
Windows 10 is now going on five years old, and Microsoft has been pushing hard over the last few years to move Windows closer to a mobile OS. When was the last time you re-imaged your phone with the corporate image? And when was the last time you worried about updating the OS on your smartphone for fear that it would break installed applications?
The idea of deploying a new flavor of Windows 10 every six months has been going down like a lead balloon with most IT departments, mostly because the multiplication effect of the work required to test applications and prepare new images. Microsoft continues to push but has extended the supported lifespan; for instance, if you deploy version 1909, and you're on the Enterprise or Education SKU, you're supported for 30 months.
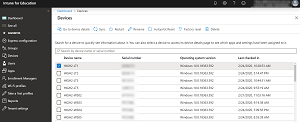 [Click on image for larger view.] Intune Device Management
[Click on image for larger view.] Intune Device Management
The basis of a modern desktop is that instead of replacing the OS with your own image, you use the Windows 10 that most OEMs deliver new devices with. It's already got the right drivers from the OEM and you can easily upgrade the Pro SKU to Enterprise during the setup. Furthermore you can use Autopilot to pre-register the devices (using a unique ID for each device) so that you can ship the device directly to the end user, and during the Out of the Box Experience (OOBE) they'll get a customized experience with your company's branding. Furthermore, using Autopilot also means that the end user doesn't become a local administrator on the PC.
Autopilot comes in a few flavors, including options to do a hybrid Azure Active Directory (AAD) and AD on-premises join, white glove and self-deploying mode. White glove lets your IT department or outsourced IT company prepare a PC fully with all applications for eventual delivery to end users, while self-deploying mode lets you set up kiosks and digital signage-type devices without providing user credentials. Finally you can also use Autopilot to reset existing devices, perhaps when they're being passed on to a different user or in an education scenario.
You then use provisioning packages to lock down configuration, upgrade the SKU of Windows and deploy applications during the setup or afterwards. At this point if you have Endpoint Manager it can take over the management of the device; alternatively you can still use GPO (if the devices are AD joined) but for a totally "modern" desktop you would use a Mobile Device Management (MDM) platform to configure the device. MDM policies do not have the many thousand settings that GPOs provide, but all the important settings are covered in most MDM solutions, including Microsoft's Intune (now also part of Endpoint Manager).
A device that's only joined to AAD and managed from the cloud using Intune presents a modern approach as it'll sit neatly in your MDM next to Android and iOS devices, and you manage all of them in a similar way. Ongoing patching can be managed by Windows Update for Business, letting you manage policies for updates from the cloud without having to deploy infrastructure on-premises for updates.
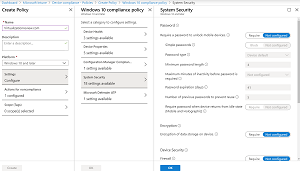 [Click on image for larger view.] Intune Compliance Policy
[Click on image for larger view.] Intune Compliance Policy
Ongoing Management
Your overall device health, upgrade readiness (for the next semi-annual release of Windows 10), application compatibility and patch status are tracked by Endpoint Manager's Desktop Analytics (replaces Windows Analytics) for your device fleet. And it uses AI to suggest which groups of devices to use for your pilot deployment of the next version of Windows to make sure you cover all applications and device hardware. Deploying Windows (and Office) upgrades in rings mimics how Microsoft does deployment across the 700+ million unmanaged Windows 10 devices that they upgrade worldwide by deploying to a small subset, closely monitoring telemetry and only rolling out to more devices when it's safe.
Another part of modern management is increasing security around identity, as it's the new security perimeter. One way to do this is to enable Multi Factor Authentication (MFA), but this is often resisted by users as it involves an extra step for logging in. Windows Hello for Business using biometrics or USB keys provides a win-win by being more convenient for users while at the same time being vastly more secure.
Another part of a modern desktop is AAD, providing cloud-based, insights-driven security decisions. Instead of providing access to applications and data simply based on a username and password, Conditional Access (CA) can take into account factors such a location of the user, the state of the device and the current risk profile of this particular user account to build graded access. If you're on a company-managed device, in the corporate office you can access all applications, whereas if you're on a personal device and not in the office you can access these applications only, and the download of data is blocked.
A modern laptop's data is protected using Bitlocker to prevent offline attacks and protected from attacks by Microsoft Defender ATP.
Conclusion
If you're an IT Pro and you're thinking that "this is all very well but I like the control I get with the old model -- I'm going to stick with it," you're in luck: The traditional way of doing corporate PCs is still supported. But I hope in this article that I've at least whet your appetite to investigate if some of these approaches could improve your life and that of your end users.
About the Author
Paul Schnackenburg has been working in IT for nearly 30 years and has been teaching for over 20 years. He runs Expert IT Solutions, an IT consultancy in Australia. Paul focuses on cloud technologies such as Azure and Microsoft 365 and how to secure IT, whether in the cloud or on-premises. He's a frequent speaker at conferences and writes for several sites, including virtualizationreview.com. Find him at @paulschnack on Twitter or on his blog at TellITasITis.com.au.