How-To
An Introduction to the AWS Security Hub
AWS is a sprawling collection of individual services, each with its own security nuances, but the AWS Security Hub is able to help with this by providing normalized security information that spans AWS services.
From the beginning, the Amazon Web Services (AWS) cloud has been based around a shared security responsibility model. Amazon is responsible for keeping the cloud infrastructure secure, while AWS subscribers are responsible for securing their own resources residing within the Amazon cloud.
One of the things that has historically made cloud security so challenging is the fact that AWS is a sprawling collection of individual services, each with its own security nuances. The AWS Security Hub is able to help with this by providing normalized security information that spans AWS services.
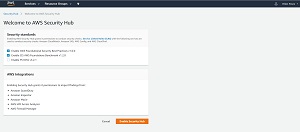
You can launch the AWS Security Hub from the AWS services menu (it's in the Security, Identity, and Compliance section). Upon launching the Security Hub for the first time, you are presented with a screen like the one shown in Figure 1 that prompts you to choose which security standards you need to adhere to. It is worth noting however, that the Security Hub cannot fully assess your compliance with these security standards. The Security Hub uses automated tests to look for various security deficiencies, but there are some aspects of the compliance process that cannot be validated through automated tests.
 [Click on image for larger view.]
Figure 1: The first step in enabling the Security Hub is to choose which security standards you need to adhere to.
[Click on image for larger view.]
Figure 1: The first step in enabling the Security Hub is to choose which security standards you need to adhere to.
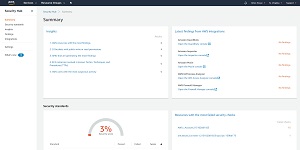
Once you have made your selections, click the Enable Security Hub button to get started. Upon enabling the Security Hub, you will be taken to a summary screen that provides an overview of the security issues throughout your organization. Figure 2 will give you an idea of what this screen looks like, although the screen capture was taken in a lab environment with no resources to monitor.
 [Click on image for larger view.]
Figure 2: The Security Hub's summary screen provides an overview of the security issues that have been detected.
[Click on image for larger view.]
Figure 2: The Security Hub's summary screen provides an overview of the security issues that have been detected.
Incidentally, AWS bills you for each automated security test that the security hub performs. Even though the per test cost is extremely low, the Security Hub can perform a surprisingly large number of tests, so it is important to keep an eye on the cost. You can find your current usage, monthly cost estimate, and pricing data by going to Settings and selecting the Usage tab, as shown in Figure 3. Although I do not recommend disabling the Security Hub, it is possible to disable it if necessary by clicking the Disable AWS Security Hub button, found on the General tab.
 [Click on image for larger view.]
Figure 3: You can find your billing information on the Settings screen's Usage tab.
[Click on image for larger view.]
Figure 3: You can find your billing information on the Settings screen's Usage tab.
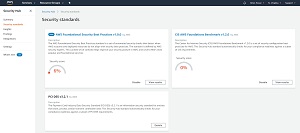
One of the Security Hub's most useful functions is its ability to compare your security against various security standards. To see how your security measures up, go to the Security Standards tab. This tab lists the security standards that you have enabled, and provides a security score for each of the standards. In Figure 4 for example, my lab environment (which is almost completely empty) yielded an AWS Foundational Security Best Practices score of 6 percent.
 [Click on image for larger view.]
Figure 4: You can use the security score to assess your compliance with various security standards.
[Click on image for larger view.]
Figure 4: You can use the security score to assess your compliance with various security standards.
If this were a production environment, such a low score would be cause for extreme concern. Fortunately, the Security Hub gives you the tools to find out why you got the score that you did, and what you can do to improve your score.
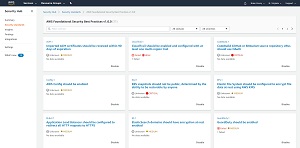
As you can see in Figure 5, the results are categorized by severity. Some of the issues shown in the screen capture are of a medium severity, while others are High or even Critical. You can filter the results based on status or on severity.
 [Click on image for larger view.]
Figure 5: The results screen shows you the various issues that have been detected.
[Click on image for larger view.]
Figure 5: The results screen shows you the various issues that have been detected.
Although the screen capture shown above might look a bit daunting, it is worth noting that the Security Hub doesn't just point out your organization's security deficiencies, it also gives you help with correcting them. Each of the issues shown in the previous screen capture are clickable. Clicking on a security issue takes you to a screen that lists the specific resources for which the issue was detected. The screen also provides a Remediation Instructions link that you can click to access step by step instructions that walk you through the process of correcting the issue. The Security Hub performs security checks on an ongoing basis, so you should eventually see your security score improve in response to any remediations that you make.
About the Author
Brien Posey is a 22-time Microsoft MVP with decades of IT experience. As a freelance writer, Posey has written thousands of articles and contributed to several dozen books on a wide variety of IT topics. Prior to going freelance, Posey was a CIO for a national chain of hospitals and health care facilities. He has also served as a network administrator for some of the country's largest insurance companies and for the Department of Defense at Fort Knox. In addition to his continued work in IT, Posey has spent the last several years actively training as a commercial scientist-astronaut candidate in preparation to fly on a mission to study polar mesospheric clouds from space. You can follow his spaceflight training on his Web site.