Report: Risk Management Lags in Changing Cloudscape
It's no secret that organizations are jumping on the cloud computing bandwagon big time, but a new report shows cloud risk management practices aren't keeping up.
"As the cloud model evolves and enterprises shift toward a heavier reliance on cloud services, it's clear that the enterprise risk management process doesn't always change with it," says the Cloud Security Alliance (CSA) in introducing a new survey-based report titled "Measuring Risk and Risk Governance," commissioned by Google.
As its name indicates, CSA is dedicated to defining and raising awareness of best practices to help ensure a secure cloud computing environment.
The not-for-profit organization's brand-new Dec. 14 report sought data on these key areas of interest:
- Assessing the maturity of public cloud consumption and risk management in enterprises
- Understanding current challenges and perceived effectiveness of risk management in public cloud
- Analyzing the challenges of measuring risk in the cloud
- Identifying best practices to reduce risk and address risk tolerance in the cloud
That effort resulted in these key takeaways:
- Cloud risk isn't keeping up with business adoption of cloud
- Organizations need to improve their digital asset management
- There is lots of room to improve risk tool satisfaction
- Monitoring, measuring, and reporting is a difficult task
"The shift to increasing workload production in the cloud and the growth in the use of cloud services is part of modernizing a business and moving towards digital transformation," the report says in discussing that first bullet-point item above about risk management not keeping up with cloud adoption. "This is evident with the cloud service usage numbers in addition to the 58 percent of survey respondent companies primarily using multiple cloud Infrastructure-as-a-Service (IaaS) providers. With cloud adoption numbers increasing, more than half (52 percent) of organizations reported not re-evaluating the risk of their cloud services being used.
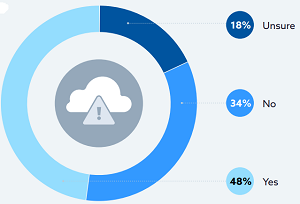 [Click on image for larger view.] Re-evaluating Risk of Cloud Services Being Used (source: CSA).
[Click on image for larger view.] Re-evaluating Risk of Cloud Services Being Used (source: CSA).
"This was often done at procurement only and does not include shadow IT services that often goes unevaluated for risk. Cloud products features and configurations change often. These products and services should be evaluated more frequently to keep up with security risks that impact the use of these products and the businesses that use them. In addition to repeated evaluation of cloud services, the risk management metrics used to evaluate cloud services should be revised. 65 percent reported adjusting risk metrics annually or longer. "
In discussing the key finding that enterprises need to improve their digital asset management, CSA said, "In fact, there is no consistency of data classification across cloud platforms and services -- only 21 percent of users are utilizing cloud service data classification, and only 65 percent of those users are aligning with internal data classification schemes."
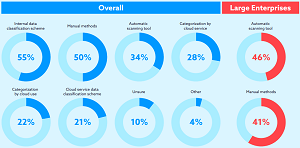 [Click on image for larger view.] Digital Asset Management Practices (source: CSA).
[Click on image for larger view.] Digital Asset Management Practices (source: CSA).
CSA also noted the lack of consistency about the identification and categorization of cloud services is exacerbated by a lack of data and cloud governance.
The organization summarized two other major findings -- both dealing with tooling -- of its report thusly:
- There is plenty of room to improve upon risk tool satisfaction. Popular risk scoring tools for quantifying or measuring risk are not meeting expectations, and open source, cloud-native, and third-party risk tools are only somewhat effective methods.
- Monitoring, measuring, and reporting is difficult. A lack of transparency, unreliable metrics, and poor reporting and forecasting tools all contribute to the difficulty.
As the graphic below shows, perhaps surprisingly, survey respondents indicated more satisfaction with open source tooling rather than cloud-native offerings or third-party products.
 [Click on image for larger view.] Risk Tool Satisfaction (source: CSA).
[Click on image for larger view.] Risk Tool Satisfaction (source: CSA).
"When it comes to monitoring, measuring, and reporting risk in the cloud, there is a vast number of tools used," the report said. "Whether cloud-native, third party, or open source, the metrics for measuring risk behind each tool are not always disclosed. The exception is open source frameworks and tools that share a defined set of criteria which may be why open source tooling was reported as more effective. Without understanding the metrics behind how risk is measured, 30 percent of enterprises reported that risk scoring systems are used as a directional guide to risk improvement for certain cloud solutions as opposed to measurements that can be relied on for comparison across all cloud services."
Other data highlights of the report include:
- Respondents were asked to estimate the percentage of workloads their organization is currently running in public cloud. The most common responses were 1-20 percent (25 percent) and 21-40 percent (25 percent). This was closely followed by 81-100 percent (22 percent).
- Multicloud strategies have been on the rise as the adoption of cloud increases. Respondents were asked about the number of IaaS platforms they primarily use. As expected the majority of respondents use 2 or more IaaS platforms (59 percent) with 24 percent using 3+.
- The primary IaaS platform(s) used by respondents unsurprisingly were AWS (65 percent) and Azure (70 percent). Google Cloud was the third most used platform (24 percent).
- To better understand the security concerns in the public cloud when running applications in the public cloud, respondents were asked to report their top three concerns. From the responses, three responses rose to the top: loss of sensitive data (64 percent), improper configuration and security settings (51 percent), and unauthorized access (51 percent). The remaining concerns received less than 27 percent.
- When asked about the vendors or tools used to quantify risk, the most common response was "None" (51 percent). Of those who indicated a vendor, there was a relatively even spread of organizations utilizing them.
- Respondents were asked whether or not they had cyber insurance coverage. Just under half reported that they did have cyber insurance. Under a third reported not having cyber insurance and under a quarter reported they were unsure.
- Respondents were asked how often they revised their risk management metrics. The most common response was "at least annually" (35 percent) followed by "at least quarterly" (22 percent).
As far as methodology for the report, it was conducted in two phases:
- Phase 1: A series of interviews were conducted by CSA from April to June 2021 based on an initial set of questions. Respondents were asked to fill out a survey and discuss their responses in detail during the interview. Data were analyzed and used to refine the question set.
- Phase 2: The refined set of questions were used to conduct an online survey by CSA from July to August 2021. Over 600 responses were received from IT and security professionals from a variety of organization sizes and locations. Data analysis was performed by CSAs research team.
"Continuously evaluating your risk status allows enterprises to properly configure and maximize the effectiveness of their security solutions, which in turn, protects their assets and improves business productivity," CSA quoted Chris Rezek, product manager/security and privacy at Google, as saying. "Yet, under half of the organizations surveyed engage in these exercises. This study has shone a light on the challenges that enterprises are facing in managing and measuring their risk, and will hopefully lead to improved risk management practices, among them centralized workflows and educating staff on how to better use the tools available to them."
About the Author
David Ramel is an editor and writer at Converge 360.