How-To
Automatically Rotating Amazon Key Management Service Keys
One of Amazon's longstanding best practices for its Key Management Service in the AWS cloud is to rotate keys on a periodic basis. This causes the key material used for cryptographic operations to be changed, thus helping to ensure that encrypted items remain private. However, although the key material is changed when a key is rotated, other attributes such as the key's ID, ARN, policies and permissions are not changed. This means that you can rotate keys without having to worry about updating your applications as would be required if you were replacing the key.
In many cases, you can configure KMS to automatically rotate keys on an annual basis. That way, you don't have to worry about remembering to rotate keys or spending time manually performing key rotations. Even so, there are a couple of limitations that you need to be aware of.
First, keys are classified as either AWS Managed or as Customer Managed. You are able to enable or disable the rotation of Customer Managed keys, but you cannot change key rotation settings for Amazon Managed keys.
Another limitation is that assuming that you are working within the GUI interface, key rotation is managed on a key-by-key basis. Amazon provides bulk actions for things like enabling or deleting keys or scheduling key deletion, but there is no bulk action for enabling or disabling key rotation.
You can enable or disable the rotation of AWS keys by logging into the AWS Management Console and then opening the Key Management Service console. You can find the Key management Service listed within the Service list's Security, Identity and Compliance section.
Once the console opens, verify that you are in the correct region and then click on the Customer Managed Keys tab. This will take you to the Customer Managed Keys screen, which you can see in Figure 1. As you can see in the figure, this screen lists all of the Customer Managed keys that exist in the current region.
 [Click on image for larger view.] Figure 1: The Key Management Service displays all of the Customer Managed keys that exist in the currently selected region.
[Click on image for larger view.] Figure 1: The Key Management Service displays all of the Customer Managed keys that exist in the currently selected region.
To change the key rotation settings for a key, click on either the key's Key ID or its alias. This will cause AWS to display the key policy and other key details. As you can see in Figure 2, there is a row of tabs about half way down the screen, and one of those tabs is called Key Rotation. Select the Key Rotation tab.
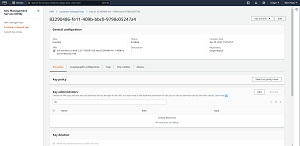 [Click on image for larger view.] Figure 2: These are the details for the selected key.
[Click on image for larger view.] Figure 2: These are the details for the selected key.
If a key is eligible for automatic rotation, then you will find a checkbox on the Key Rotation tab that you can select in order to automatically rotate they key on an annual basis. You can see what this looks like in Figure 3. Simply select the checkbox and click the Save button.
 [Click on image for larger view.] Figure 3: Select the Automatically Rotate This KMS Key Every Year to enable automatic key rotation.
[Click on image for larger view.] Figure 3: Select the Automatically Rotate This KMS Key Every Year to enable automatic key rotation.
You may occasionally find that the Key Management tab is missing. If that happens, then go back to the screen shown in Figure 1 and take a look at the Key Spec column. This column should contain a value of SYMMETRIC_DEFAULT. This indicates that the key is a symmetric, single encryption key that can be used for both encryption and decryption operations. The reason why this is important is because automatic rotation can only be enabled or disabled for symmetric keys. You cannot change the automatic rotation settings for asymmetric keys. Instead, AWS displays a Public Key tab in place of the Key Rotation tab. You can see the tabs that exist for asymmetric keys in Figure 4.
 [Click on image for larger view.] Figure 4: There is no automatic key rotation for asymmetric keys.
[Click on image for larger view.] Figure 4: There is no automatic key rotation for asymmetric keys.
It is worth noting that asymmetric keys are not the only type of keys for which automatic key rotation is not supported. You won't be able to use automatic key rotation for any key that contains imported material or that resides in a custom key store. Even so, you can manually rotate such keys.
About the Author
Brien Posey is a 22-time Microsoft MVP with decades of IT experience. As a freelance writer, Posey has written thousands of articles and contributed to several dozen books on a wide variety of IT topics. Prior to going freelance, Posey was a CIO for a national chain of hospitals and health care facilities. He has also served as a network administrator for some of the country's largest insurance companies and for the Department of Defense at Fort Knox. In addition to his continued work in IT, Posey has spent the last several years actively training as a commercial scientist-astronaut candidate in preparation to fly on a mission to study polar mesospheric clouds from space. You can follow his spaceflight training on his Web site.