How-To
Microsoft Cloud App Security: Everything You Need to Know
Are you protecting your business users with firewalls? The same firewall that you've been using for a few years? Do you feel confident that it's protecting you against today's risks?
If not, you may need to augment your approach with a solution for today's Software-as-a-Service (SaaS) cloud services world -- a Cloud Access Security Broker (CASB). Microsoft has one such cloud-based solution, Microsoft Cloud App Security (MCAS).
In this article we'll look at what MCAS can do for your business, how it integrates with other security technologies and the different flavors it's available in. We touched briefly on MCAS in earlier articles: A Look at Security in the Microsoft Cloud and Review: Azure Advanced Threat Protection and Advanced Threat Analytics.
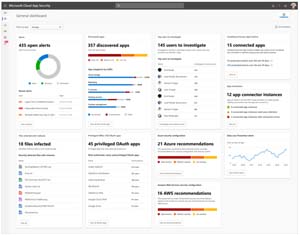 [Click on image for larger view.] MCAS Dashboard
[Click on image for larger view.] MCAS Dashboard
Favorite Flavor
There are three different versions of MCAS: Office 365 Cloud App Security, Azure Active Directory Cloud App Discovery and Cloud App Discovery. As you might deduce from the name, the first one comes with Office 365 E5 licensing and provides a subset of capabilities, with manual upload of logfiles only (see below) and Threat Detection, Conditional Access and Information Protection for Office 365 workloads only. The Azure AD version is part of AAD Premium P1 licensing (itself part of Microsoft 365 E3 licensing) and does both manual and automatic log uploads but doesn't provide Information Protection or Threat Detection.
 [Click on image for larger view.] MCAS Architecture (Courtesy of Microsoft)
[Click on image for larger view.] MCAS Architecture (Courtesy of Microsoft)
How MCAS Works
MCAS gives you a catalog of over 16,000 cloud apps that it'll look for in the firewall/proxy logs that you upload to it and it'll discover (hence the name) the apps that are in use in your environment. For each of these apps you'll see traffic volumes across internal IP addresses and users on an ongoing basis. For each app you can do a risk assessment, based on the rich information in the catalog, and identify services that you want to sanction (and probably bring into Azure Active Directory to be published for single-sign-on and governance) and others that you want to un-sanction/block.
 [Click on image for larger view.] Cloud App Catalog
[Click on image for larger view.] Cloud App Catalog
For each service there's in-depth information such as when they were founded, hosting datacenters, security configuration and policies, along with legal and compliance information. The catalog (available in all three flavors of MCAS) alone is worth the price of admission; a poor security admin that's given a list of 50 different cloud services in use by the organization and asked to rank them by trustworthiness would spend weeks gathering this information. You can also alter the weights that make up the score between 1 and 10 that each service receives, perhaps your business doesn't care about FedRAMP but GDPR compliance is crucial, for example.
 [Click on image for larger view.] Cloud Service Information
[Click on image for larger view.] Cloud Service Information
Additionally, you can control data uploads and downloads to any app for Data Loss Prevention (DLP) and also integrate with Azure Information Protection. The former works both with the built-in DLP engine in Office 365 as well as third-party DLP solutions. An example of the latter would be automatically identifying a Word document being uploaded to Dropbox as containing sensitive information (credit-card numbers, for one example, but it could be any type out of 100 different templates) and applying a sensitivity label to it ("Confidential") and protecting it with encryption and restricting access to internal employees only.
You can also use the supplied templates to detect anomalous behavior such as mass downloads by a single user, public sharing of confidential files, odd mailbox rules, impossible travel and deletion of multiple VMs in Azure, AWS or GCP, along with many other potential threats.
To feed the insights and machine learning engine behind MCAS it needs log data. This can be uploaded from your on-premises firewalls or proxy servers (all major brands supported), or Zscaler, iboss, Corrata and Microsoft Defender ATP (MDATP). Or you can use a custom log format.
The other main integration point is connecting MCAS to cloud service APIs for apps such as:
Depending on the capabilities of each API, you can set up policies to detect and respond to malware, unusual file sharing/deletion activities or unusual administrative activities.
The integration with MDATP deserves extra mention as many IT pros dismiss "Windows Defender" as a basic antivirus solution (which was true a few years ago), but today Microsoft Defender provides full-fledged Endpoint Detection and Response (EDR), machine learning-based agents for Windows, Mac, Linux and, in public preview, Android.
The integration with Windows 10 is particularly powerful. Taking only a minute to configure, it enforces your sanctioned/blocked cloud apps on any endpoint (whether they're connecting from the corporate office or from home), enforces policies and uploads logs from each endpoint to MCAS. In essence MDATP acts as an agent for MCAS without you having to deploy anything.
Another feature that I think is going to become increasingly important is the ability to enforce policies around OAuth apps. Recently here in Australia there's been a heightened focus on the use of "fake" applications that pretend to be a real service (for instance MailGuard 365, a popular email hygiene service here) that tricks users into accepting various OAuth permissions, giving the attackers "legitimate" access to data, often flying totally under the radar of the defenders.
 [Click on image for larger view.] Manage OAuth App Permission Policies
[Click on image for larger view.] Manage OAuth App Permission Policies
Integrations
Apart from the MDATP integration, MCAS also integrates with Azure Advanced Threat Protection. This excellent cloud service, born out of the on-premises application Advanced Threat Analytics (ATA), uses agents in your on-premises Active Directory (AD) environment to identify malicious attackers as they gain a foothold and start moving laterally, eventually compromising privileged accounts. Laser focused on AD, it provides high-fidelity signals that are now integrated into the MCAS console for easy correlation with other identity-based incidents.
MCAS also works with Azure AD Identity Protection, which uses machine learning-based analysis to identify risky users and risky sign-ins to AAD, letting you apply policies based on identity risk signals. Furthermore MCAS also integrates tightly with Conditional Access (CA), the AAD technology that's used to evaluate access to particular resources based on who the user is, what groups they're a member of, the security posture of the device they're using and whether it's a managed or unmanaged device. CA lets you build a zero-trust approach to security.
MCAS also uses the logs generated in Azure Security Center, a service in Azure that applies policies and protections for your cloud-deployed Infrastructure-as-a-Service (IaaS) and Platform-as-a-Service (PaaS) resources. MCAS is updated several times per month, with new features coming at cloud speed. Here's a good source for understanding your licensing options with MCAS.
Conclusion
If you don't have a CASB in place for your business today you need to take a good, hard look at where the data and applications that run your organization are located and how you're protecting them. The days of relying solely on a "blinky light firewall" to give you a sense of security are gone, and you need a cloud-based security solution for controlling your users' cloud access.
About the Author
Paul Schnackenburg has been working in IT for nearly 30 years and has been teaching for over 20 years. He runs Expert IT Solutions, an IT consultancy in Australia. Paul focuses on cloud technologies such as Azure and Microsoft 365 and how to secure IT, whether in the cloud or on-premises. He's a frequent speaker at conferences and writes for several sites, including virtualizationreview.com. Find him at @paulschnack on Twitter or on his blog at TellITasITis.com.au.