Everyday Virtualization
How To Set Active Directory Authentication with vCenter Server Appliance
One thing that is a must for most organizations is to join the vCenter Server to Active Directory. A few words of advice to do this smoothly.
- By Rick Vanover
- 05/28/2014
Last year when I wrote 10 Steps to Setting Up vCenter Server Appliance The Right Way, the First Time, I wrote it more as a note to myself to get it set up correctly. I used the post to check a number of things that were more difficult to get correct with the vCenter Server Appliance in versions prior to vSphere 5.5.
With vSphere 5.5, a lot of those steps are now unnecessary as the appliance has most of the settings now correctly configured by the deployment settings. What made it confusing before was that the wizard for configuring the vCenter application appeared right on the first page of the appliance, even though the pre-requisite steps needed to be done first.
I've been using the vCSA almost exclusively in new situations and have become a fan of the new configuration. Primarily, I prefer to use the vCenter application rather than administer the database and more. (I've spewed a few choice words at the vCenter database running on SQL Server over the years.)
One thing that is a must for most organizations is to join the vCenter Server to Active Directory. If you want to add it to Active Directory, the first thing to do is sure that the DNS server and suffix on the vCSA are correct. Once you double-check those, enter the format of the domain and the credential in the vCSA (see Fig. 1).
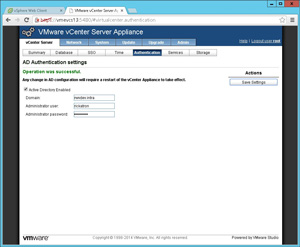 [Click on image for larger view.]
[Click on image for larger view.]
Figure 1. The domain configuration is set in the vCSA.
I'll again admit that I'm blogging this to partly ensure I remember the steps to join to the domain. Specifically, do we put the domain name in FQDN or short name (NetBIOS) format in the fields? Of course it's the FQDN, and the next question I always forget is whether to put DOMAIN\Username format in place. That too isn't needed, as it's implied by the domain name. The vCSA needs a reboot to make this take effect, so make sure that is done at a time that a brief vCenter outage can be taken.
Assuming the DNS, host name and suffix configuration of the vCSA are correct, you'll also be able to add your appliance to the domain. Note that this step adds a computer account for the vCSA. No Group Policy objects can be applied to it, but don't let some non-involved admin disable or delete that computer account because they don't know what it is. By default it will go in the \Computers OU.
Setting up Active Directory will require the certificate for the vCSA be regenerated; it's an easy step in the vCSA configuration (the 5480 port web interface), as shown in Fig. 2.
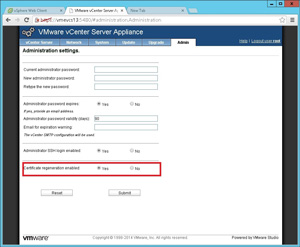 [Click on image for larger view.]
[Click on image for larger view.]
Figure 2. The certificate needs to be regenerated, then the vCSA rebooted.
After that, you'll need to log into the vCSA as [email protected] (it's in default configurations) instead of the root account to configure vCenter Single Sign-On to use the Active Directory groups. But that's not all! You'll need to reconfigure the identity source if you want to use Active Directory for security constructs within Single Sign-On. Specifically, we'll need to remove it and re-add it, as shown in Fig. 3.
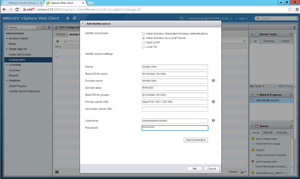 [Click on image for larger view.]
[Click on image for larger view.]
Figure 3. The domain configuration will correctly allow group enumeration when configured as shown here.
At this point, we now have Active Directory groups in the vCenter application. We can log in to the vSphere Web Client; we can put the group in native SSO groups and more! (See Fig. 4.)
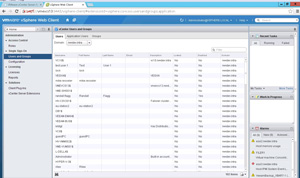 [Click on image for larger view.]
[Click on image for larger view.]
Figure 4. Now, the Active Directory domain contents are visible in the vSphere SSO section of the Web Client.
Configuring the vCSA to use Active Directory is indeed a process, but once you get it set up it's ready to go. Have you learned any tricks along the way? Share your comments here.
About the Author
Rick Vanover (Cisco Champion, Microsoft MVP, VMware vExpert) is based in Columbus, Ohio. Vanover's experience includes systems administration and IT management, with virtualization, cloud and storage technologies being the central theme of his career recently. Follow him on Twitter @RickVanover.