How-To
SSH on Windows 10
With the OpenSSH client now installed by default on Windows 10, Tom Fenton explaines what SSH is and why it is so popular, how to use it, and what configurations can be done with it, before doing the same for Secure Copy (SCP).
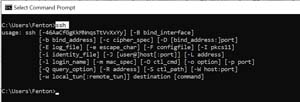
For 20 years now, I have used Secure Shell (SSH) to connect to servers and transfer files from one system to another. Although SSH has been a standard feature on Unix and Linux, I have had to use third-party SSH products, such as PuTTY, to get SSH functionality on Windows systems in the past. The other day, I accidentally entered ssh in the command prompt on a Windows system, and much to my surprise I was greeted with a usage prompt. I did not realize that with the April 2018 update, the OpenSSH client is now installed by default on Windows 10. In this article, I will explain what SSH is and why it is so popular, how to use it, and what configurations can be done with it. I will then go on to do the same for Secure Copy (SCP).
 [Click on image for larger view.]
[Click on image for larger view.]
SSH is an extremely handy OS-independent network protocol that is secured via cryptographic means for operating network services over an unsecured network, and uses a client-server architecture. I first became aware of SSH as a replacement for telnet, but quickly found that it could also be used to execute commands remotely, copy files from server to server, and even act as a mechanism for tunneling and forwarding TCP ports.
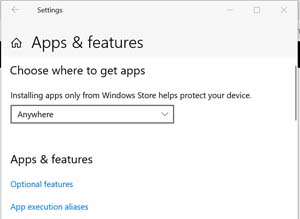
As noted above, the SSH client is now installed by default in current versions of Windows 10. You can verify that your Windows 10 version has it enabled by opening Windows Settings and navigating to
Apps > Optional features and verifying that
Open SSH Client is shown. If it is not installed, you may be able to do so by clicking
Add a feature.
 [Click on image for larger view.]
[Click on image for larger view.]
 [Click on image for larger view.]
[Click on image for larger view.]
Because SSH uses a client server architecture, it does require that an SSH server be running on the other server in order to be used. Fortunately, all major OSes have SSH servers.
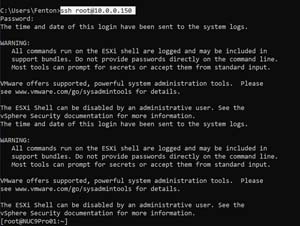
In the examples below, I will be connecting to an ESXi system that has an SSH server running on it from my Windows 10 machine (but these commands will be identical for other SSH systems). I will first show each command’s generic usage and then an example(s) of its actual usage.
The first and most common usage for SSH is to remotely log in to a remote system:
- ssh user@]host[:port] <- The default port is 22
- ssh [email protected] <- You will be prompted for a password
 [Click on image for larger view.]
[Click on image for larger view.]
For security and liability reasons, the ESXi system that I logged in to replied with a warning security message.
You can also run commands remotely using SSH:
- ssh [user@]host[:port] remote command
- ssh ssh [email protected] ls /vmfs/volumes/ <- This lists the contents of the directory
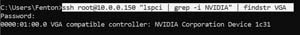
- ssh [email protected] "lspci | grep -i NVIDIA" <- Quotes are needed for complex commands
 [Click on image for larger view.]
[Click on image for larger view.]
You can also pipe the commands to a local command, or save the output to a local file:
- ssh [email protected] "lspci | grep -i NVIDIA" | findstr VGA <- findstr is a Windows command and is processed locally
- ssh [email protected] "lspci | grep -i NVIDIA" > MyOutput <- The output is saved to a local file
 [Click on image for larger view.]
[Click on image for larger view.]
 [Click on image for larger view.]
[Click on image for larger view.]
Using SCP
SCP uses the same security mechanism as SSH, but rather than running commands, it is most commonly used to securely copy files from one system to another:
- scp source user@host:/location /i>
- scp .\TestFile [email protected]:/tmp <- Transfers TestFile to a tmp directory on a remote server
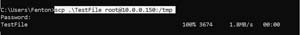 [Click on image for larger view.]
[Click on image for larger view.]
SCP is a rich tool that can has many options. A few that are commonly used are -l to limit the bandwidth (in KiB) that SCP will consume, -p to preserve the modification times, access times, and modes from the original file, and -v for verbose mode which is useful for debugging issues with SCP. You can see all the options for SCP by entering scp /?.
 [Click on image for larger view.]
[Click on image for larger view.]
Conclusion
SSH and SCP have become staples in most Unix and Linux system administrators’ toolboxes, and I am happy to see that Microsoft has now included them by default with Windows. Also, since SSH depends on an SSH server to connect to, I am glad to see that Microsoft now includes an SSH server with Windows 10; in my next article, I will show you how to install and configure it.
About the Author
Tom Fenton has a wealth of hands-on IT experience gained over the past 30 years in a variety of technologies, with the past 20 years focusing on virtualization and storage. He previously worked as a Technical Marketing Manager for ControlUp. He also previously worked at VMware in Staff and Senior level positions. He has also worked as a Senior Validation Engineer with The Taneja Group, where he headed the Validation Service Lab and was instrumental in starting up its vSphere Virtual Volumes practice. He's on X @vDoppler.