News
Misconfigurations Continue to Plague Cloud Security, New Reports Say
Several years ago Amazon Web Services (AWS) was bedeviled by a series of high-profile and highly publicized data breaches due to user misconfigurations, and new reports indicate the problem persists to this day in the industry.
Back in the AWS spree, many misconfigurations allowed access to S3 buckets, while others had to do with firewall misconfigurations.
While the seemingly unending series of AWS reports have abated greatly since then, misconfiguration is still a problem.
Sonrai Security, in announcing its new report, "The State of Enterprise Cloud Security: The Good, The Bad, And The Ugly," said the study "revealed what enterprises see as the key contributors to cloud breaches -- many related to identity and misconfiguration."
Meanwhile, a report from the Cloud Security Alliance, "State of Cloud Security Concerns, Challenges, and Incidents," said the same thing. The CSA said its new survey "finds that 58 percent of respondents are concerned about security in the cloud, while misconfigurations are one of the leading causes of breaches and outages, as public cloud adoption doubles over past two years."
Yes, despite all the publicity, increased guidance from major cloud platforms and others, along with numerous outreach and education attempts, users are still leaving their organizations open to data breaches, attacks or outages.
Sonrai Security identified cloud misconfiguration as a "growing problem," saying it stood out as a leading cause of breaches, with 37 percent of survey respondents reporting that data breaches had increased significantly in the last 12 months.
Top reasons they occur include:
- The complexity of their cloud environments (53 percent)
- Lack of education and training (45 percent)
- Too few IT and security staff members (43 percent)
- Unexplained human error (29 percent)
"The concern is both timely and well-supported, with a recent report from Gartner Research ['Managing Privileged Access in Cloud Infrastructure' Published 9 June 2020] estimating that, 'By 2023, 75 percent of security failures will result from inadequate management of identities, access, and privileges, up from 50 percent in 2020.'"
Again, the CSA study concurred.
"Cloud issues and misconfigurations are leading causes of breaches and outages: Eleven percent of respondents reported a cloud security incident in the past year with the three most common causes being cloud provider issues (26 percent), security misconfigurations (22 percent), and attacks such as denial of service exploits (20 percent)."
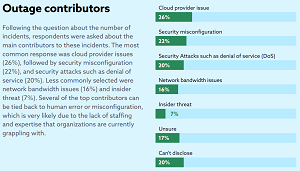 [Click on image for larger view.] "Several of the top contributors can
be tied back to human error or misconfiguration" (source: CSA).
[Click on image for larger view.] "Several of the top contributors can
be tied back to human error or misconfiguration" (source: CSA).
Of course, such misconfigurations are just among many cloud security issues detailed in the reports.
Key findings of the CSA report were summarized by the organization thusly:
- Security tops concerns with cloud projects: Respondents' leading concerns over cloud adoption were network security (58 percent), a lack of cloud expertise (47 percent), migrating workloads to the cloud (44 percent), and insufficient staff to manage cloud environments (32 percent). It's notable that a total of 79 percent of respondents reported staff-related issues, highlighting that organizations are struggling with handling cloud deployments and a largely remote workforce.
- Nearly one-third still manage cloud security manually: Fifty-two percent of respondents stated they use cloud-native tools to manage security as part of their application orchestration process, and 50 percent reported using orchestration and configuration management tools such as Ansible, Chef and Puppet. Twenty-nine percent said they use manual processes to manage cloud security.
- Who controls cloud security is not clear-cut: Thirty-five percent of respondents said their security operations team managed cloud security, followed by the cloud team (18 percent), and IT operations (16 percent). Other teams such as network operations, DevOps and application owners all fell below 10 percent, showing confusion over exactly who owns public cloud security.
Sonrai Security said that in addition to cloud misconfigurations, outside hackers and insider threats, the most common -- and often overlooked -- contributors to data breaches included:
- Overprivileged Identities: Identities with significantly more privileges and access than are required to carry out the duties assigned to them introduces a significant risk to the cloud.
- Human Error: Human mistakes will happen and will not be deliberate at times, but these errors can still wreak havoc in an organization. One example we commonly see is an employee who takes shortcuts leaving sensitive data in locations where it is not adequately protected.
- Unauthorized Access: Due to the complex nature of cloud environments, having visibility into which identities have access to data and resources is increasingly difficult. Organizations need to secure all crown jewel data and enforce policies to prevent unauthorized access to the cloud environment.
Coincidentally, Virtualization & Cloud Review just yesterday reported on yet another new cloud security study -- from CloudKnox -- in the article "Study IDs Permissions Risks in Major Cloud Platforms," which also mentioned minconfigurations. "The Cloud Permissions Gap is a contributing factor to the rise of both accidental and malicious insider threats as attackers are able to exploit an identity with misconfigured permissions and access your critical cloud infrastructure," the report stated.
The Sonrai Security study was based on survey data from Osterman Research. The 101 respondents reportedly had a minimum of $50M in annual revenue and 1,000 employees.
The CSA said its survey polled almost 1,900 IT and security professionals from a variety of organization sizes and locations, with the goal of gaining deeper insight into the complex cloud environment that continues to emerge, growing more complex amid the pandemic. The survey was announced by CSA and AlgoSec, described as "a leading provider of business-driven network and cloud security management solutions."
The CSA said it's dedicated to defining and raising awareness of best practices to help ensure a secure cloud computing environment.
Sonrai Security said it's the leader in identity and data security for public cloud.
See the links above more information on survey findings and demographics.
About the Author
David Ramel is an editor and writer at Converge 360.