In-Depth
Cooking with Azure Virtual Desktop
A bit of a hidden gem, Azure Virtual Desktop can address several end user computing problems, including some that are extra salient in today's IT world. This article will explain the basics of what it is, where it fits and where it doesn't, why you should care and improvements that are coming soon.
The Need
Do you have situations where users work from home, connecting from personal devices? Do you trust those devices and the networks they're connecting from? Do you have compliance regulations that require strict controls over local storage on PCs of data, something that's hard to achieve with normal client computers?
The solution might be virtual desktops. Of course, these solutions aren't new, and we've been doing two flavors of this on-premises for a long time. The first is Remote Desktop computing where a Windows server serves out desktops for multiple users to connect to. Windows Server offers T̶e̶r̶m̶i̶n̶a̶l̶ S̶e̶r̶v̶i̶c̶e̶s̶ Remote Desktop Session Host (RDSH), and of course Citrix is known for their offerings. The second flavor is Virtual Desktop Infrastructure (VDI) where you spin up virtual machines (VMs)-- on Hyper-V or VMware -- and each user is assigned their own VM with Windows client running in it. Some years ago, there were many different hopefuls in this space. Microsoft had some cobbled-together solutions, while VMware offers Horizon.
Both these flavors have a lot of overhead in terms of infrastructure and know-how and require continuous maintenance.
I've recently been implementing different Proof-of-Concept (PoC) projects for two of my clients, one involving Windows 365 and one involving Azure Virtual Desktops, so I'll also share some lessons I've learnt along the way.
 [Click on image for larger view.] Azure Virtual Desktop Session Hosts
[Click on image for larger view.] Azure Virtual Desktop Session Hosts
Add Cloud and Mix
Unsurprisingly, the rise of public cloud computing has tackled this space from several different angles, AWS offers WorkSpaces, Google provides Virtual desktops and Microsoft has two offerings in the market: Windows 365 and Azure Virtual Desktop (AVD). The former is a Software-as-a-Service (SaaS) version of AVD, with a dead-easy configuration, simple pricing (just pick your Cloud PC size and pay a fixed price per user per month) and limited configuration options.
The biggest thing to consider here is as soon as you put distance between the end user device and the desktop they're interacting with, you add latency. Yes, modern hyperscale clouds have amazing networking and nodes in nearly every major city on the planet, but latency is a fact of life. This means the success of remote desktop solutions depends heavily on the type of applications used, the individual user's connection quality to the internet/the cloud datacenter and your configuration settings.
Microsoft does have a couple of aces up its sleeve when it comes to these services, in particular the introduction of Windows 10 (and now 11) Multisession. This is a special version of the Windows client that allows multiple users to connect to the same VM and each get their own desktop. This neatly bypasses one of the issues that arose with RDSH and comparable solutions that relied on running Windows Server to serve multiple desktops -- application compatibility. Sometimes an end user application isn't happy running on a server OS. Windows Multisession, only available in Azure Virtual Desktop (not on-premises or in another cloud) neatly bypasses the app compatibility issue.
The second ace is Microsoft's long experience with remote desktop computing. The first version was introduced in Windows NT 4, and, essentially, Azure Virtual Desktop is a hosted version of the same building blocks that make up RDSH on premises.
Azure Virtual Desktop Ingredients
There's Web access gateway, which in AVD ensures that no RDP port is open to the internet, always performing a reverse connect operation back to the client when you try to connect. There's the Broker, which picks which VM to connect you to the first time and later reconnects you to the same session if you get disconnected/return another day. Diagnostics of both health and performance is built in (via an Azure Monitor Insight) and management is done through the usual Azure tools, web portal, PowerShell, CLI or API. All these components are managed by Microsoft as part of the service.
Your responsibilities include image management (if you're bringing your own Windows images, rather than using the built-in marketplace ones), profile management (see below), user management and identity (Azure AD), sizing, scaling and access management. You need to create at least one host pool, with at least one session host VM in it, and you can pick from any of the VM sizes Azure offers. The recommended size of the VM depends on the number of users per VM and the type of user workload they generate (light, medium, heavy and power user) but it should have at least four vCPUs and no more than 24. It's better to add more hosts to cater to more users, as it's easier to schedule restart of hosts for maintenance if you have more of them. There's also little performance gain after 24vCPUs. If you have a requirement to provide graphics acceleration in the session VMs, there are several VM series that come with high end GPUs such as the NVv4 (AMD Radeon Instinct MI25 GPUs) or the NVv3 (NVIDIA Tesla M60 GPU).
There are two main flavors of AVD: personal or pooled desktops. With personal, each user is assigned their own VM that they're always reconnected to and can optionally be a local administrator on (think developers or engineers that need a "beefy" machine all to themselves). With pooled, each user is connected to a random session from those available on any session host and their user profile (Windows settings, configuration, files, OneDrive files and so on) is stored outside of the VM. The technology to store user profiles for a pooled session host pool is called FSLogix (based on an acquisition by Microsoft some years back). It creates a VHD(X) file for each profile which is attached to the session at the time of login, so the experience is transparent to the user. However, this makes it easy to backup these profiles (if required) and to update or replace the Windows 10/11 desktop separately to the user profiles.
Using MSIX app attach you can also create VHD files of the applications you want to provide to the users and attach them in the same way as the user profiles at the time of login, simplifying app deployment significantly. You can also do MSIX app attach on any normal Windows 10/11 PC.
 [Click on image for larger view.] Monitoring Azure Virtual Desktop Performance
[Click on image for larger view.] Monitoring Azure Virtual Desktop Performance
Network connectivity to AVD can be over the public internet from anywhere (remember, no open RDP port) or confined to Site to Site VPN/ExpressRoute connectivity from on-premises to Azure. If you have full control over the network path (or assign a public IP address to the session host VMs), you can use RDP Shortpath to swap from TCP to UDP for greater performance.
Clients are available for PC, macOS, iOS and Android, plus a web client that'll work in any HTML 5-capable browser. Note that the built-in remote desktop client in Windows (mstc.exe) doesn't work with AVD/Windows 365. You can also publish individual applications instead of a full desktop using AVD, where the user simply runs an application side by side with their local applications, but it's actually running on a session in AVD.
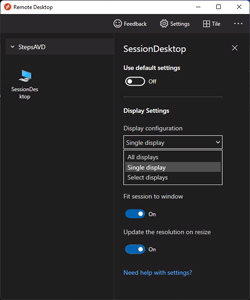 [Click on image for larger view.]The Windows Remote Desktop Client Monitor Settings
[Click on image for larger view.]The Windows Remote Desktop Client Monitor Settings
Access to AVD sessions can be gated using Conditional Access policies, including ensuring that each connection involves a Multi-Factor Authentication (MFA) prompt.
Generally, audio and video meeting software and remote desktops don't work well together (capturing the audio and video on the local PC, then sending it to the AVD desktop in the cloud and then on to the other participants in the meeting introduces too much latency). However, Microsoft Teams get special treatment with optimizations that increase the performance with some limitations (720p video only, for example).
Add AD DS, Azure AD or Azure AD DS and Fry Lightly
One of the most confusing parts of AVD is the plethora of options and flexibility you have when it comes to setup and configuration. Of course, this means you can craft the exact right solution for a particular company, but it also means there are lot of choices to make in your designs.
Today, AVD relies on Active Directory Domain Services (AD DS). The VMs are domain joined, but the users signing into them need to have accounts in Azure Active Directory. You can achieve this in a few ways. First, you can have a network connection to on-premises from the VMs in the cloud, so that they can see your on-premises Domain Controllers (DCs). You also need to synchronize all relevant user accounts on-premises to an Azure AD tenant in the cloud, not a huge leap for many organizations as they're already doing this for their Microsoft/Office 365 tenant. Another option is to run DCs in VMs in Azure; again they'll need some way to synchronize with your DCs on-premises. A third way is to use the managed Azure Active Directory Domain Services (AADDS -- I kid you not) offering what is essentially two DCs that are managed by Microsoft that you don't have direct access to. In this scenario, your user accounts are synched from on-premises AD DS to your Azure AD tenant, and then from there to AADDS.
The end goal, however, is to remove the reliance on AD DS altogether.oday you can have VMs that are only joined to Azure AD, but only for personal desktops with local profiles. The second part is the current preview of Kerberos support in Azure AD, which will enable access to FSLogix profiles without relying on AD DS file permissions. This means a full cloud solution is quite close, but not here yet.
Windows 365 Is the Topping
Unlike the extreme flexibility offered by AVD, Windows 365 is very straightforward. There are two flavors (notice a theme?), Business for organizations up to 300 users and Enterprise where you can supply your own images, easily connect to on-premises networks and integrate fully with Endpoint Manager (Intune). There's only the personal type of desktop, though. A user is assigned a Cloud PC through a license, and that is their desktop until you re-assign the license to someone else. And it's always on, unlike in AVD where you scale session hosts up and down based on the load to save on the running costs of VMs.
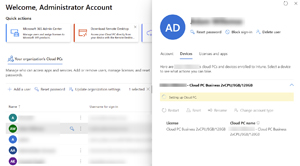 [Click on image for larger view.] Windows 365 Admin Center
[Click on image for larger view.] Windows 365 Admin Center
My Experience
The AVD PoC deployment at my client has been in place for a quite few months and was initially implemented to manage sudden COVID-19 lockdowns here in Australia for some staff at a ~350 user organization. As Australia's response to COVID-19 has radically changed, this has seen less usage over the last few months. We used a site-to-site VPN for this client to provide line of sight to the on-premises DCs and in fact force all network traffic back on-premises for inspection by their edge firewall. The main lesson and challenge for me has been the sheer number of configuration tweaks that are possible, but it's in a good place now, and should it be required in the future we can easily scale this solution out to offer secure desktops to hundreds of staff in a few hours.
The second client, a small financial services firm, has just started migrating from their current Windows Server 2016 RDSH server (hosted in Azure) to Windows 365. The scaling of the RDSH host, and management of when it should be turned on for staff to work and turned off to save on running costs, is a constant challenge. Their reliance on a central server for their main LOB applications is also significantly reduced as they've spent the last year migrating to a SaaS-based alternative, and now only need server access for historical data access.
The challenge in this project has been the lack of AD DS -- they don't have an Active Directory infrastructure. The RDSH host relies on local accounts and everything else is managed through Azure AD. This has brought some challenges around managing their Cloud PCs using Intune, but a support call solved this (the assigned user must be made a local administrator and the device manually enrolled in Intune, after which the user can be reverted to a standard user).
 [Click on image for larger view.] A Cloud PC in Microsoft 365 Lighthouse
[Click on image for larger view.] A Cloud PC in Microsoft 365 Lighthouse
The nice thing about Windows 365 Business is that it can be managed in the new Microsoft 365 Lighthouse portal.
Conclusion
In the right scenario, remote desktop computing definitely brings some good benefits, and, as you have seen, Microsoft offers flexibility to meet most needs your organization might have.