News
Ransomware Payoffs Becoming 'Cost of Doing Business,' Report Says
New research from Cohesity indicates many organizations are breaking "do not pay" policies and paying off ransomware demands, writing off the payments as the "cost of doing business."
Paying off threat actors is generally not advised, but many organizations do it just to get back in business (see "Ransomware Payouts Can Be 'A Matter of Life or Death' but 'Don't Pay' Generally Advised").
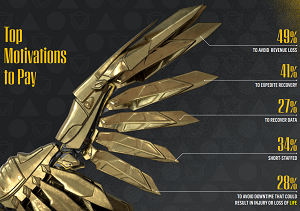 [Click on image for larger view.] Top Motivations to Pay (source: Cybereason).
[Click on image for larger view.] Top Motivations to Pay (source: Cybereason).
What's more, "paying off" doesn't necessarily pay off, as a 2022 report from Veeam found that many victimized organizations paid ransoms and recovered their data. However, nearly as many either recovered their data without paying the ransom or paid the ransom and still didn't recover their data (see "Survey Shows Limits of Ransomware Insurance, Payoffs").
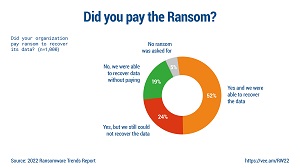 [Click on image for larger view.] Did You Pay the Ransom? (source: Veeam).
[Click on image for larger view.] Did You Pay the Ransom? (source: Veeam).
Nevertheless, the payoff practices continue amid the years-long ransomware deluge, said the data security and management specialist, citing new research it commissioned that polled 902 IT and security decision-makers in Australia, the United Kingdom and the United States.
Those decision-makers paint a bleak ransomware picture, according to these company-supplied highlights of the study:
-
The threat of cyberattacks is a real, rising, rampant crisis:
- Almost all respondents said the threat of cyberattacks to their industry will increase in 2024 compared to 2023, with 71 percent expecting the threat to rise by over +50 percent y/y
- Most respondents reveal their organization has been a victim of ransomware in the prior 6 months to being surveyed.
- The exact same percentage of respondents express concerns about their company's cyber resilience strategy
-
Paying ransoms is becoming a 'cost of doing business' for many:
- More than 9 in 10 said their company would pay a ransom to recover data and restore business processes
- 9 in 10 have paid a ransom in the last two years, despite the vast majority having a 'do not pay' policy or protocol
- Over two-thirds of respondents said their companies would be willing to pay over $3m to recover data and restore business processes, and of these 2 in 3 over 50 percent said their company would pay over $5m
-
Data recovery capabilities are not fit for purpose and undermine cyber resilience (the ability to continue usual business operations despite suffering an adverse cyber event):
- No respondent said their company could recover data or business processes after a cyberattack in 24 hours or less
- Less than half of respondents said their organizations could recover and restore business processes in under 7 days.
- 2 in 3 respondents say their company's CIO and CISO could be better aligned.
A Cohesity news release provides more details on the research.
About the Author
David Ramel is an editor and writer at Converge 360.