Generative AI was married with Raspberry Pi soon after the whole craze started, but now it's official.

Brien Posey provides step-by-step instructions for creating a firewall to prevent or allow specific DNS queries.

Ransomware specialist Veeam Software announced a new cloud storage service to securely store backup data off-site in an always-immutable and encrypted format, just as the firm published a new ransomware trends report.

Tom tests the desktop hypervisor recently made free for personal use to students, hobbyists and casual users who want to run multiple OSes on a single computer.
Shortly after rumors of a tiff with AWS, Broadcom has strengthened its VMware ties with rival cloud giant Microsoft Azure, with the companies yesterday announcing plans to support VMware Cloud Foundation subscriptions on Azure VMware Solution.

Tom steps through the process of downloading, installing and licensing Workstation Pro 17 on his personal laptop.
The PwC 2024 AI Jobs Barometer report analyzes over half a billion job ads to reveal the transformative impact of AI on job growth, skills demand, wage premiums and productivity across various sectors.

Tom Fenton explains how this is huge news for the tens of thousands of students, hobbyists and casual users who would like to run multiple instances of OSes on a single computer.

Microsoft extended its small language model (SLM) technology along with cloud-based large language models (LLMs) to the device level with the introduction of Copilot+ PCs, which leverage powerful processors and multiple state-of-the-art AI models.

As expected, the kickoff of Google I/O 2024 was heavy on the AI, with new updates for the company's cloud-based Vertex AI service leading a slew of day 1 announcements centered around generative AI.

Tom recaps an end-user computing conference heavy on the tech (no sales) featuring "choose your own adventure" and what to pack for bug-out bags for tech emergencies.

IBM is jumping on the Copilot AI assistant bandwagon popularized by Microsoft with a new IBM Copilot Runway initiative.
OpenAI is working on a Model Spec document that specifies desired behavior for its models in its API and ChatGPT.
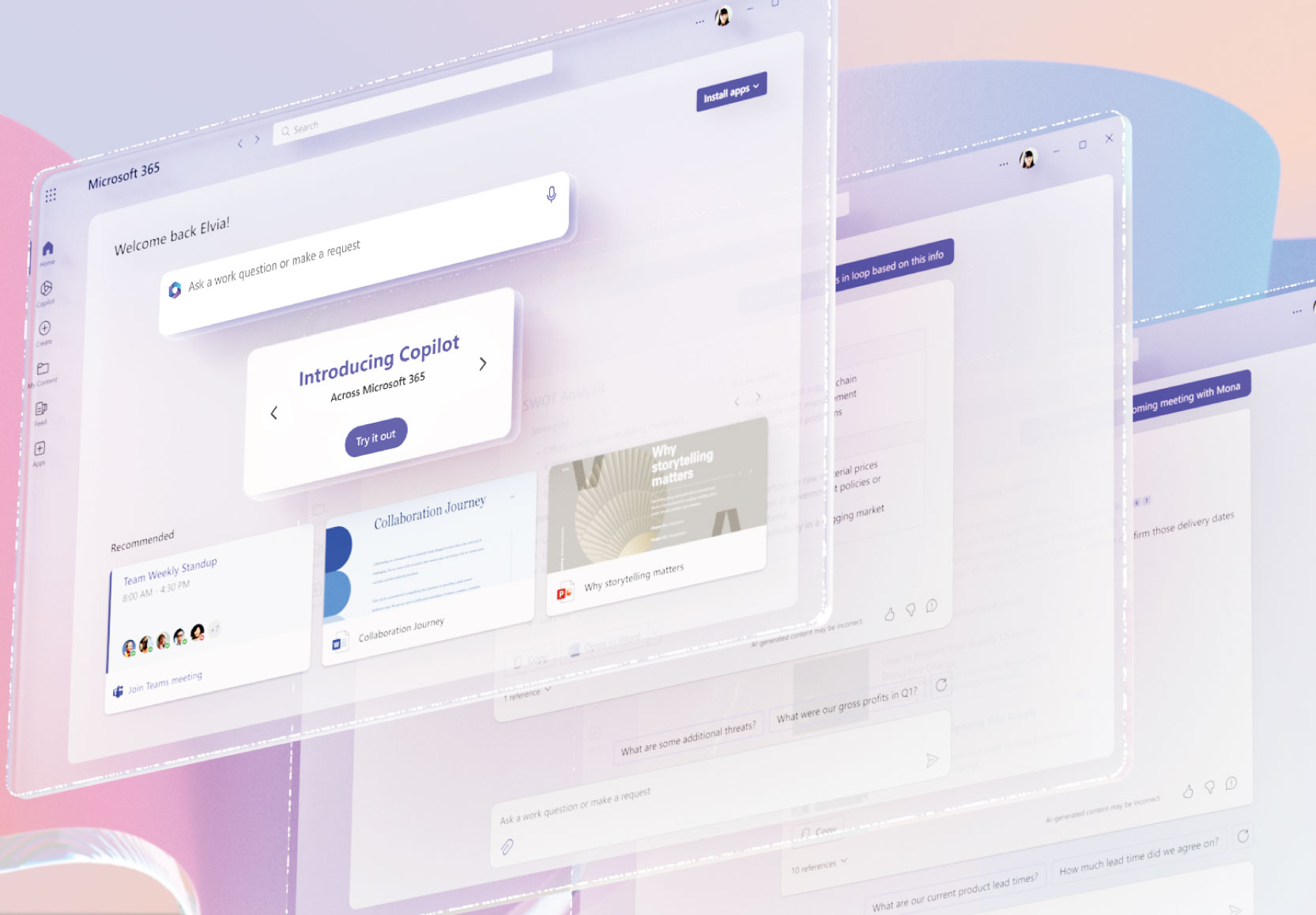
In announcing its fourth annual Work Trend Index report yesterday, Microsoft teased AI features coming up for Microsoft 365, its cloud-based productivity suite.

Microsoft published a 2024 Work Trend Index delving into the "state of AI at work," finding that many employees are increasingly hungry for AI tools and won't wait for their employers to provide them.

New Gartner research on providers of cloud AI developer services shows the usual cast of characters leading the pack.

During this week's RSA Conference, the CSA announced new guidance for organizations to successfully implement AI, with recommendations focusing on security and compliance.

"We are acting quickly to correct this misinformation because, as Winston Churchill correctly said, 'A lie gets halfway around the world before the truth has a chance to get its pants on.' "

Frustrated by outdated info? Here's a roundup of the knowledge cutoff dates and internet search abilities of some top freely available online AI sites.

Brien Posey explains how to use the AWS Tools for PowerShell to make AWS services accessible through the PowerShell interface, providing extra capabilities.