How-To
Setting Up and Working with Amazon WorkSpaces, Part 2
After previously writing about different options available to use Active Directory services with WorkSpaces, Tom Fenton details how he set up his WorkSpace.
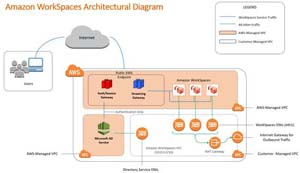
This is the second article in a series on WorkSpaces, Amazon's Desktop-as-a-Service (DaaS) solution. In the previous article, I wrote about the different options available to use Active Directory (AD) services with WorkSpaces. In this article, I will show you how I set up my WorkSpace, and in the next article, I will go over how I set up and used AWS Simple AD for AD services for these WorkSpaces.
 [Click on image for larger view.]
[Click on image for larger view.]
When setting up my WorkSpaces environment, I used Amazon's Amazon WorkSpaces Proof-of-Concept document for reference. When I reviewed the document, I found some things that were new to me and/or would be a little confusing for Amazon Web Services (AWS) newbies, so below I documented the experience I had setting it up.
This article assumes that you understand general IT concepts, like security, subnetting, and routing, and also have a basic level of familiarity with the following AWS-specific technologies: Amazon Virtual Private Cloud (VPC), and Amazon Elastic Compute Cloud (Amazon EC2). It also assumes that you have an AWS account already set up.
Setting up an External IP Address
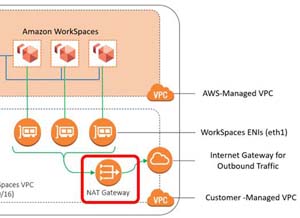
A WorkSpaces environment needs a routable Elastic IP address. This IP address is used for its Network Access Translation (NAT) gateway, which enables outbound internet access by WorkSpaces via their private subnets, thereby preventing the internet from initiating a connection with them.
 [Click on image for larger view.]
[Click on image for larger view.]
You can create an Elastic IP address via the Amazon Virtual Private Cloud (VPC) Console by selecting Elastic IPs from the left menu, then clicking Allocate Elastic IP address and Allocate. Be sure to make note of the IP address and its ID.
 [Click on image for larger view.]
[Click on image for larger view.]
WorkSpaces VPC
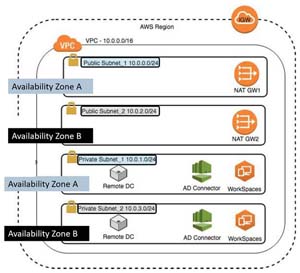
For the WorkSpaces environment, you will need to create a VPC with two public and two private subnets. For demonstration purposes, I will use the same naming convention as that in the AWS POC documentation.
Users access their WorkSpaces by using a VDI client. After a user is authenticated, streaming traffic is initiated through the streaming gateway. Each WorkSpace will have two elastic network interfaces associated with it: Eth0 is used for management and streaming, and Eth1 is used for outbound traffic.
 [Click on image for larger view.]
[Click on image for larger view.]
Public Subnet_1 and Private Subnet_1 will be in one Availability Zone, and Public subnet_2 and Private Subnet_2 should be in a different Availability Zone. Be sure to make a note of the VPC ID as it will come in handy later when you create the environment.
 [Click on image for larger view.]
[Click on image for larger view.]
To create these subnets, I used the VPC Wizard following the instructions in the Amazon POC documentation.
 [Click on image for larger view.]
[Click on image for larger view.]
One problem that I had with the documentation is it didn't give examples of the IPv4 CIDR blocks to use, so I used the defaults from the diagram above, and put them in the table below:
| |
10.0.0.0/16 |
|
|
| Public Subnet_1 |
10.0.0.0/24 |
us-west2a |
WorkSpaces Public Subnet 1 |
| Private Subnet_1 |
10.0.1.0/24 |
us-west2a |
WorkSpaces Private Subnet 1 |
| Public Subnet_2 |
10.0.2.0/24 |
us-west2b |
WorkSpaces Public Subnet 1 |
| Private Subnet_2 |
10.0.3.0/24 |
us-west2b |
WorkSpaces Private Subnet 1 |
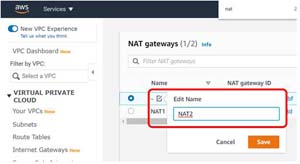
The documentation says to edit the name of the NAT gateway. To do this, point to the name cell and click the edit icon.
 [Click on image for larger view.]
[Click on image for larger view.]
It is critical that the subnets and routing tables are set up correctly. Below is a screenshot of how mine are set up.
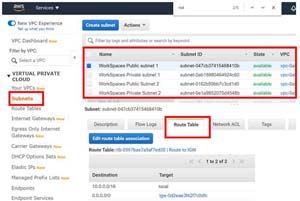 [Click on image for larger view.]
[Click on image for larger view.]
Conclusion
Although the POC document was very helpful in setting up my environment, certain aspects of the process took some thinking and exploring on my behalf to figure them out; I tried to document these problematic areas in this article. In my next article in this series, I will show you how I provided AD services and deployed WorkSpaces.
Here's Part 3: Setting Up and Working with Amazon WorkSpaces, Part 3
About the Author
Tom Fenton has a wealth of hands-on IT experience gained over the past 30 years in a variety of technologies, with the past 20 years focusing on virtualization and storage. He previously worked as a Technical Marketing Manager for ControlUp. He also previously worked at VMware in Staff and Senior level positions. He has also worked as a Senior Validation Engineer with The Taneja Group, where he headed the Validation Service Lab and was instrumental in starting up its vSphere Virtual Volumes practice. He's on X @vDoppler.