News
App Security Report: Open Source Code Still 'Blessing and a Curse'
A new Veracode report on application security finds that while things are generally getting better, some persistent problems remain, including the use of flawed open source and third-party code libraries.
That finding comes in the 12th State of Software Security report from the application security testing specialist. The report is based on data collected from Veracode services and customers, including millions of scans of various types. The report includes findings about applications that were subjected to static analysis, dynamic analysis, software composition analysis and/or manual penetration testing.
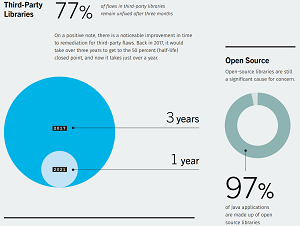
"Open source libraries are still a significant cause for concern," the report says, referencing a persistent and well-documented problem that continues today. Part of that persistence might be attributable to developer habits.
"Most developers stick with the same libraries year over year," says one section of the the report, while another says, "history is teaching us that we will experience the same types of flaws year after year."
Nevertheless, the report notes that third-party libraries now have fewer flaws and that they're getting addressed faster.
"On a positive note, there is a noticeable improvement in time to remediation for third-party flaws. Back in 2017, it would take over three years to get to the 50 percent (half-life) closed point and now it takes just over a year."
 [Click on image for larger view.] Third-Party, Open Source Stats (source: Veracode).
[Click on image for larger view.] Third-Party, Open Source Stats (source: Veracode).
In addition to looking at the use of software analysis tools and analyzing flaws in software, the report examines how flaws are fixed and looks into the future of secure software. Overall, things are looking up, as the report says, "The trend across all the applications is a general reduction in flaw prevalence."
However, Veracode noted, increased connectivity of all kinds and the rise of connected, distributed microservices have complicated the app security picture.
"But it's not just increased connectivity that's shaping the security landscape -- it's the hypercompetitiveness and the need to constantly innovate," the report says. "To move faster, many development teams have turned to native cloud technologies, microservices architectures and open source code to accelerate and scale their efforts. Additionally, development teams have adopted agile methodologies and are automating as many steps in the development process as possible.
"While this evolution increases the speed of the software development lifecycle, it also introduces new complexities and risks."
Some highlights of the report include:
- Microservices: In 2018, roughly 20 percent of applications incorporated multiple languages. This year, less than 5 percent of apps used multiple languages, suggesting a pivot to smaller, one-language applications or microservices.
- The number of apps scanned has tripled: Organizations are scanning, on average, more than 17 new applications per quarter. This number is more than triple the number of apps scanned per quarter a decade ago.
- Organizations are using multiple types of scanning: We've seen a 31 percent increase in the use of multiple scan types between 2018 and 2021, with much of that gain coming from organizations using the full suite of static, dynamic and SCA scans.
- Most developers stick with the same libraries year over year: We found that developers stick with tried-and-true libraries and rarely attempt to refactor their code base to pick up the "coolest" or "most-popular" libraries.
Those specific data points lead to four generalizations about the report's findings:
- Agile development of small, modular applications has eaten the world. We've seen an explosion in the number of applications being scanned. We've seen developers move from scanning their applications once a quarter to once a day, as well as expand their use of different scanning technologies.
- Free and open-source code will continue to be a blessing and a curse for developers. We see no signs that the use of third-party libraries has changed dramatically, or even the libraries developers are using. Developers appear to be using fewer libraries with known flaws and that's cause for optimism.
- Applications are, slowly but surely, getting more secure. What is perhaps most heartening throughout this analysis is that, nearly across the board, we've seen steady progress toward more secure applications. While some subsets of flaws have increased in prevalence over time, the trend has generally been downward. This is impressive, given that the capacity for and speed of fixes hasn't necessarily increased. We're hopeful this trend will carry on and that the future will continue to look bright.
- New tools will continue to help improve the application security landscape. In the past, we've noted that using different types of scanning means that developers will fix all types of flaws faster and more completely. Having these types of tools built into continuous integration pipelines and IDEs will only speed developer adoption.
"Security debt can build over time and addressing it early can help mitigate work down the road," Veracode said. "Using multiple types of scanning -- static, dynamic and software composition analysis -- can give a fuller picture of an application's security and it helps remediation happen more quickly and more completely."
About the Author
David Ramel is an editor and writer at Converge 360.