News
Microsoft Ups Its Virtual Desktop Game As Usage Spikes During COVID-19
Microsoft, like other vendors of virtual desktop services, has seen an increase in usage as the COVID-19 pandemic has caused millions of workers to abandon office buildings and work from home.
In response, the company this week announced that a Spring Update to its Windows Virtual Desktop (WVD) service has entered a public preview.
"Due to the global health crisis, many people are working remotely for the first time," said an April 30 blog post authored by Microsoft execs. "We’ve been humbled by the number of you who have used Windows Virtual Desktop to meet the needs of your increasingly distributed and remote workforce."
WVD got commercially launched back in September. It's a virtual desktop infrastructure service for remotely accessing client desktops and applications. Organizations using WVD can access true Windows 10 or Windows 7 operating systems and applications, which run on virtual machines housed in Microsoft Azure datacenters. It typically requires having Microsoft 365 E3 or E5 licensing to use the WVD service, per the pricing page.
Microsoft hasn't said a lot about the WVD service since its September launch. However, this week there was plenty of news.
WVD and ARM Integration
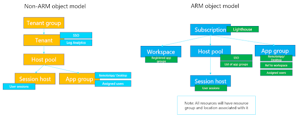
It turns out that despite its origins on Azure, WVD wasn't quite a true Azure service, according to the announcement. The spring update preview aims to change that situation. It's enabling WVD "objects" to become resources within Azure Resource Manager (ARM). ARM is a Microsoft management solution that's used across various Azure cloud-based services.
 [Click on image for larger view.] Moving to ARM (source: Microsoft).
[Click on image for larger view.] Moving to ARM (source: Microsoft).
Here's how the announcement explained that point:
Up to this point WVD has not been an Azure Resource Manager service. But rather the WVD objects have all existed within a separate database. With the Spring Update all WVD objects now are ARM resources in their own right.
The switch to using ARM resources with the WVD spring update preview is expected to make things easier when deploying and managing the WVD service -- at least for new WVD tenancies. However, organizations already using the WVD service likely will have to roll up their sleeves and make various configuration changes, as described in the announcement, if they want to take advantage of enhancements enabled by the spring update preview.
One good bit of news is that organizations can now use the Azure Portal to make those WVD configuration changes. However, they'll first need register the WVD ARM resource provider in the Azure Portal to get access.
"As WVD is now an ARM object you need to register the Windows Virtual Desktop ARM Resource Provider," the announcement explained. "This enables you to interact with the service that orchestrates WVD within the ARM service."
Seasonal WVD Updates
The announcement noted that even though Microsoft is calling this release the WVD spring update preview, that's a somewhat artificial designation since Azure services get updated on a continual basis and "Azure does not have versions." Nonetheless, Microsoft may stick with this seasonal update naming convention for future WVD releases.
"Expect future continuous updates to be dropped into platform in the future in a similar manner, with some larger updates getting some kind of seasonal naming," the announcement explained regarding coming WVD updates.
Benefits of ARM Integration
WVD tenancies will get some benefits from WVD becoming an ARM service with the spring update preview. It'll be possible to publish applications to Azure Active Directory groups, for instance.
In addition, IT pros will be able to use the Azure Role Based Access Control (RBAC) service for controlling access to IT organizational resources.
Additionally, as mentioned above, the integration with ARM lets IT pros use the Azure Portal to manage a WVD tenancy.
"Prior to the Spring Update the options to manage a WVD tenant was, PowerShell or a simple Management App Service Web App, or a third party tool," Microsoft's announcement explained.
The integration with ARM is also generally positive in terms of WVD tooling support. ARM provides a common API for Azure PowerShell, Azure Command-Line Interface and REST clients, in addition to the Azure Portal, making them all work similarly, according to Microsoft's "What is Azure Resource Manager?" document.
On the PowerShell front, organizations have needed to use an RDS (Remote Desktop Services) PowerShell module for WVD tasks. Microsoft has now replaced it with an Azure module, called "AzWvd," which is available in PowerShell Core.
Another benefit of the ARM integration is that it permits WVD tenancies to have a "dedicated scale-out capability" for WVD host pools. The current scale-out process without the spring update preview is much less straightforward. Here's how the announcement described the current WVD host pool scaling approach:
Prior to the spring update if you wanted to scale out a host pool you would run the Azure Marketplace deployment or the Github template a second time and reference the existing Resource Group and Host pool. You would specify the number of VM's you wanted to end up in the host pool, i.e. 10. If your host pool had five VMs it will deploy five VMs to make up the difference.
Options for monitoring the WVD service also expand with the ARM integration. Instead of having to use "either PowerShell or another Diagnostics App Service Web App" to monitor WVD, organizations can use Log Analytic in the Azure Portal and run Kusto queries. The results can be integrated into Power BI reports, as well.
Organizations having "data sovereignty" concerns about where the WVD service stores data will be able to select regional locations, starting with the spring update preview. This ability to designate the "service metadata storage location" for WVD is just at the beginning stages, though. It'll kick off in the United States first, followed by Europe and other regions later, the announcement indicated.
WVD Security and Compliance Recommendations
If that weren't enough, Microsoft described some security and compliance recommendations for WVD tenancies in a Thursday announcement by Brad Anderson, corporate vice president for Microsoft 365, and Julia White, corporate vice president for Microsoft Azure.
They recommended using the Azure Firewall service with WVD for "Internet egress directly from Azure," as well as "limiting the outbound connections." Organizations can use the "WindowsVirtualDesktop service tag, which limits internet egress traffic from your VMs to specific IP addresses in Azure," the announcement indicated. A service tag is used instead of a specific IP address when creating security rules, per Microsoft's description.
Another security and compliance recommendation was to use "reverse connect technology" with WVD. "Reverse connect significantly reduces the attack surface area by letting you run a virtual machine (VM) without keeping any inbound ports open," the announcement explained.
Organizations also can use "FSLogix profile containers" to enhance security. "Profile containers provide a simple, robust solution to quickly manage virtual profiles in non-persistent environments while staying protected through your organization's security settings," the announcement indicated. Microsoft specifically bought FSLogix's roaming profiles solution to facilitate these sorts of remote access scenarios.
WVD Linux Thin Clients
Microsoft also has plans to expand client support for the WVD service. WVD desktop clients are currently available on Android, iOS, Mac and Windows platforms, as well as HTML5 browsers, but Microsoft is currently developing a new SDK that will open up Linux thin-client options.
"In addition to these platforms, we're releasing a new Windows Virtual Desktop software development kit (SDK) to our development partners to support the creation of Linux-based thin clients" for the WVD service, the announcement indicated.
Release timing of the new SDK wasn't indicated, though.
About the Author
Kurt Mackie is senior news producer for 1105 Media's Converge360 group.