News
'Tighter & Tighter' Cyber Insurance Regs: Assertions, Attestations and Reimbursements
Insurance companies really don't want to actually provide the services you pay them for.
You learn that if you're a corporate policy holder victimized by a ransomware attack. If that's the case, hopefully you've dotted all your I's and crossed all your T's and have enough money in the bank to pay the ransom before asking your vendor for a reimbursement to avoid what could be a multimillion-dollar loss.
"Insurance companies are for profit, and they are losing a lot of money on cyber insurance right now," says John O'Neill Sr. "So they're trying to tighten up those losses and make it make it harder for them to lose money when they pay out on these claims."
The chief technologist at AWS Solutions was sharing his front-line knowledge -- along with partner Dave Kawula at TriCon Elite Consulting -- with hundreds of attendees in this week's half-day, online summit presentation by Virtualization & Cloud Review on Modern Hybrid Cloud Security. In discussing best practices for hybrid cloud infrastructure, he explained that insurance companies are cracking down on their attendant regulations, such as requiring a third-party attestation form be filled out or asserting that Multi-Factor Authentication (MFA) is used everywhere.
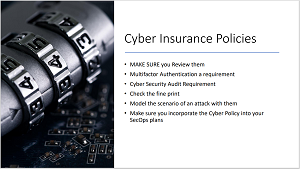 [Click on image for larger view.] A High-Level Cyber Insurance Polices Checklist
[Click on image for larger view.] A High-Level Cyber Insurance Polices Checklist
And, even if those I's are dotted and T's are crossed, policy holders who decide to pay a ransom still have some hurdles to leap, as they must come up with the cash up front and then just hope for a successful reimbursement claim.
"The insurance company doesn't provide it like a checkbook as you go along," O'Neill Sr. said. "You have to pay it out and then get them to reimburse you. And on the reimbursement, they send in -- you can think of it as an adjuster, but it's a forensic specialist -- that then takes all the assertions that you the IT team made during your application, such as 'Do you have MFA on all Remote Connectivity accounts?' And they come in and they find that vendor VPN account ... and they say, 'wait a minute, this one doesn't have it.' And here's the IT pro who thinks that there's an opportunity here for you to justify that or explain that.
 "And I've actually seen it -- personal experience -- where someone had coverage and lost a $4 million claim based on that (IT pro falsely saying MFA was applied to all accounts)."
"And I've actually seen it -- personal experience -- where someone had coverage and lost a $4 million claim based on that (IT pro falsely saying MFA was applied to all accounts)."
John O'Neill Sr., chief technologist, AWS Solutions
"And I haven't seen that, in one single instance, be the case where you could provide an explanation for why you said 'yes, all accounts have it,' but you didn't actually apply it to all accounts. In those cases the insurance company denies the claim and your company doesn't get reimbursed. And I've actually seen it -- personal experience -- where someone had coverage and lost a $4 million claim based on that. And I don't want to be the IT guy that answers the question that says, 'hey, we have an MFA on all accounts.' And then we need to get $4 million reimbursement and I have to look at my company and go, 'Yeah, well, I answered that, yes, but it really wasn't true. And they denied our claim.' That probably wouldn't work out too well for me. So I just recommend to people don't do that."
Kawula noted that insurance companies are adjusting their policies according to Common Vulnerabilities and Exposures (CVE) that may be present in a policy holder's infrastructure, which, when found, can act as a "get out of jail free" card for vendors reluctant to pay out. The CVE provides a reference-method list of publicly known information-security vulnerabilities and exposures. Insurers have begun to implement sliding scales that impose premium penalties for CVE items found in a policy holder's infrastructure depending on how soon systems were patched after specific CVE items became known and were added to the list, like this example:
- N-30-60 Days – 0% Premium Penalty
- N-61-90 Days – 25% Premium Penalty
- N-91-180 Days – 50% Premium Penalty
- +365 Days – No Coverage
"Because remember, the insurance industry is a for-profit industry," Kawula said.
 "And so they want to make it hard on you to get paid out, and that's just been the insurance game forever. And so nothing has changed.."
"And so they want to make it hard on you to get paid out, and that's just been the insurance game forever. And so nothing has changed.."
Dave Kawula, managing principal consultant, TriCon Elite Consulting
"And so they're not going to just kind of hand out payments without some type of criteria," he continued. "And so they want to make it hard on you to get paid out, and that's just been the insurance game forever. And so nothing has changed. But with all of the ransomware attacks that have occurred through the the most terrible global pandemic in history, with COVID-19, we've seen such an uptick in cyber threats come through the landscape that the amount of customers getting hit with ransomware attacks and stuff, they've had to pay out a lot."
O'Neill Sr. agreed while revisiting the new CVE-related restrictions. "The insurance companies are getting tighter and tighter on the CVE, and patch deployments, right? And so the U.S. government, like when it comes to Windows updates or patches, they require that you have those things deployed to systems within three weeks. And insurance companies, what I'm noticing, are following suit. So a lot of them have requirements that say, 'Hey, patches have to be required, or have to be implemented within X amount of time-frame from their release by a vendor,' and you can't justify why you don't do it. If you don't do it, that's fine with them, they just won't cover you. They won't offer you a policy.
"And what we're finding is that they will have started implementing a sliding scale where they say, 'Okay, well, if you implement it within 14 days, you're fine. If you implement it, somewhere between 14 and 30 days and have an event, we're only going to cover 80 percent of your policy limit. If you implemented after 30 days, but before 90 days, we're going to cover you at 50 percent and so on and so forth.' I have actually seen some insurance underwriters specify that if you don't have a patch installed, on all identified systems ... I've seen policies where if you don't have that done within the 90-day period, your coverage drops to zero. So I expect that to continue and to increase in tightness over the coming years."
Kawula also cautioned about IT pros trying to come up with perfect infrastructure security designs, because they don't exist, and O'Neill Sr. likened that situation back to cyber insurance.
"We can get so tied up and wanting to be perfect, that we have absolutely leave a bunch of holes that create our own demise," O'Neill Sr. said. "And you know, that a lot of that comes to some of the insurance and the security issues that are out there. Everybody thinks they have to be perfect to get coverage. And so they answer questions wrong, or inconsistently, or that kind of thing. And I've found that unfortunately, that's a really bad approach."
Rather, he said, IT pros should be completely up front and honest when negotiating with insurance vendors.
"If you don't meet something, what I found is most effective is go into it with complete transparency with the insurance broker that you're working with, or the auditor, whatever it is, and say, 'Hey, we don't meet this,' but then come to them with a plan on how you're going to meet it. And when you're going to be able to meet it and that kind of thing. Usually, in my experience, they will work with you. Then you might get a policy to a lower limit than you expected. Your premium might be higher, but you'll still get the policy. And that's better than the [other] outcome. And I know a lot of IT people don't believe this. But this is the reality. I've seen it a dozen times this year already."
The Kawula/O'Neill Sr. presentation is available for on-demand viewing, but live summits provide other benefits, such as Q&A with the presenters (not to mention a spiffy prize awarded to one lucky attendee). With that in mind, upcoming events this month include:
The full list of future and on-demand summits can be found here.
About the Author
David Ramel is an editor and writer at Converge 360.