In-Depth
Data Expert Details How Cyber Resilience Starts Where Backup Strategy Ends
Organizations that still think a solid backup strategy is enough are missing the bigger challenge, according to Karen Lopez, who said the real test is whether systems can be restored quickly, safely and in a way that keeps the business running.
In a session at today's online tech-education summit, "Beyond Backup: Building a Modern Disaster Recovery Framework," Lopez argued that cyber resilience requires a broader mindset than traditional security or backup planning.
 "Being able to restore a system doesn't mean the business has recovered."
"Being able to restore a system doesn't mean the business has recovered."
Karen Lopez, @datachick.bsky.social
Her presentation, "Designing a Cyber Resilience Plan that Actually Works," focused on what organizations need to do after prevention fails. In addition to her Microsoft MVP status, Lopez is a data management expert, ADGP and Microsoft Certified Trainer. Her presentation is being made available for on-demand replay thanks to the sponsor, Rubrik, which also presented at the summit.
Rather than treating resilience as a new label for familiar security practices, Lopez framed it as a shift in priorities. "The difference, in my mind, between cybersecurity and cyber resilience is we're moving. We still have to prevent and protect, but we're moving a lot of focus on recovery and adaptation." She then made the underlying premise explicit: "focusing on recovery and adaptation means we know for sure that something bad is going to happen in our systems at some point."
Backup Is Only the Starting Point
One of the clearest themes in Lopez's talk was that backup should be treated as one piece of a larger recovery program, not as proof that an organization is ready. Her discussion of secure backup strategy emphasized multiple copies, offsite protection, restore validation and tighter separation between backup administration and production access.
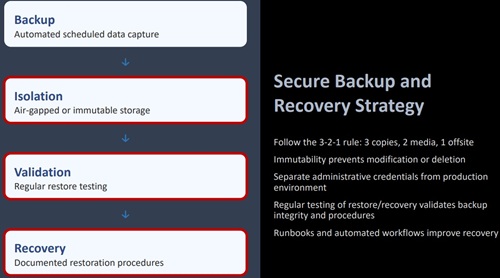 [Click on image for larger view.] Secure Backup and Recovery Strategy (source: Karen Lopez).
[Click on image for larger view.] Secure Backup and Recovery Strategy (source: Karen Lopez).
Lopez said immutable or otherwise isolated backup storage remains important, but she also cautioned that this addresses only part of the problem. In the audience Q&A, she noted, "When I say it protects it, I mean from somebody deleting it, manipulating it, corrupting it. That doesn't protect access." Her larger point was that backup integrity still has to be paired with stronger identity and access controls.
She also drew a sharp line between storing backups and proving that recovery actually works. "Being able to restore a system doesn't mean the business has recovered," she said, summarizing one of the central ideas of the session.
Recovery Plans Need To Be Tested, Not Filed Away
Lopez spent substantial time on backup testing and validation, arguing that resilience plans have to be exercised, measured and refined instead of sitting untouched in documentation. That means scheduled restore and failover exercises, testing for different failure scenarios and measuring whether recovery targets can actually be met.
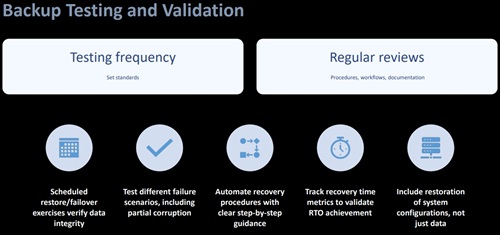 [Click on image for larger view.] Backup Testing and Validation (source: Karen Lopez).
[Click on image for larger view.] Backup Testing and Validation (source: Karen Lopez).
She said organizations should test not only routine restores but also partial corruption scenarios and configuration recovery, especially as more services move into cloud and managed environments. Automation, in her telling, is not just about speed. It is also about reducing avoidable mistakes when teams are under pressure.
Recalling earlier recovery work, Lopez contrasted manual restoration with tested playbooks and repeatable automation. "Now, if I can run a playbook that I've tested, that I've validated, I'm just sitting there sipping my coffee, watching it happen."
Failover Has To Be Planned in Advance
Lopez also devoted significant attention to failover design, describing resilience as a combination of health checks, automated failure detection, traffic redirection and verification that the failover itself succeeded.
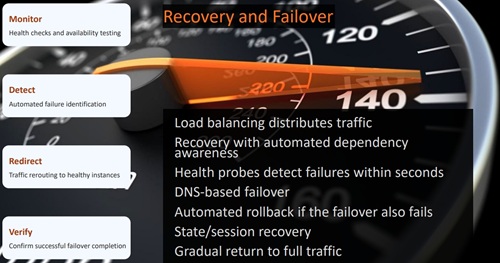 [Click on image for larger view.] Recovery and Failover (source: Karen Lopez).
[Click on image for larger view.] Recovery and Failover (source: Karen Lopez).
Her explanation went beyond generic backup advice. She discussed automated dependency awareness, DNS-based failover, rollback if the failover also fails, and the need to stage the return of traffic instead of turning everything back on at once. She also pointed to the risk of recovery surges, where queued workloads, reconnecting users and delayed jobs can overload recovering infrastructure and create a second problem during the recovery process.
The practical takeaway was that organizations need to design recovery for real operating conditions, not just for an ideal restore scenario on paper.
Technical Recovery and Business Continuity Have To Meet
Another of the talk's stronger sections focused on the relationship between technical recovery and business operations. Lopez said IT teams have traditionally concentrated on restoring servers, databases and applications, while business units separately figured out how to keep orders moving, customers informed and workarounds in place.
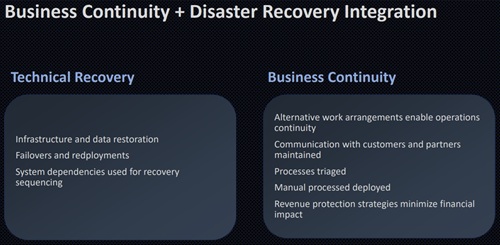 [Click on image for larger view.] Business Continuity + Disaster Recovery Integration (source: Karen Lopez).
[Click on image for larger view.] Business Continuity + Disaster Recovery Integration (source: Karen Lopez).
That split no longer works, she said. Recovery exercises should combine technical failover with business continuity planning, because the organization needs both. It is not enough to recover infrastructure if the surrounding business process has not been thought through.
That same theme came through in the Q&A when she was asked how to decide whether recovery speed matters more than recovery completeness. "That is a business decision," she said, adding that technical teams need to show decision-makers the tradeoffs in time, cost and impact rather than assuming those decisions belong to IT alone.
By the end of the session, Lopez's message was straightforward: backup still matters, but it is only the beginning. Real cyber resilience depends on whether organizations can test recovery, automate repeatable steps, fail over cleanly and keep the business operating when prevention does not hold.
And More
And, although replays are fine -- this was just today, after all, so timeliness isn't an issue -- there are benefits of attending such summits and webcasts from Virtualization & Cloud Review and sister sites in person. Paramount among these is the ability to ask questions of the presenters, a rare chance to get one-on-one advice from bona fide subject matter experts (not to mention the chance to win a free prize, in this case $10 Starbucks gift cards, provided by Rubrik. With all that in mind, here are some upcoming summits and webcasts coming up:
With all that in mind, here are some upcoming summits and webcasts coming up from our parent company in the next month or so:
About the Author
David Ramel is an editor and writer at Converge 360.