News
Don't Get Fired: How to Sell Max Cybersecurity to the C-Suite
"Nobody is gonna get fired for buying too much security in today's day and age."
Those wise words come from IT consultant Dave Kawula, speaking in a recent presentation on hybrid cloud security.
But, while you won't get fired for buying too much security, you might get fired for not buying enough security. And you might get fired for not buying enough security even after you recommended such a buy to C-suite suits who turned you down for financial reasons. Then you get hit with a multimillion dollar ransomware attack and the suits are looking for heads to roll, having forgotten all about nixing your request.
Guess what? Their heads aren't going to roll.
See, there's an art to dealing with the C-suite on security budgets and requests: You have to both convince them and protect yourself in the process.
"Where you will get fired," Kawula continued, "is where you're going to have the opportunity to implement [max security] and you chose not to, because of a cost -- because when the business comes back to you, and they say, 'Well, you didn't really explain the threat well enough; if we would have really known that it was this serious, we would have pulled the trigger on that PO.' Don't get yourself to that point."
With that, he turned the presentation over to his partner, John O'Neill Sr., who is practiced in the art of C-suite negotiations to convince execs not to shoot themselves in their corporate feet, asking for his thoughts on the maximum level of protection that you should provide for infrastructure.
"I'm chuckling a little bit, because I don't think there is a maximum, right?" replied O'Neill Sr. "You have to do exactly like you said, and you have to layer and layer upon layer, and you have to articulate risk. Because exactly what you described is exactly what I've seen happen over and over. I've seen IT people, who I know, went to their bosses went to their management and said, 'Hey, you know, we have a risk over here, we need to buy this thing.' And, 'No, we just don't have the budget for it,' or whatever. And then when the bad event happens, management forgets that that discussion ever occurred. And they describe it exactly as you did, 'Well, you just didn't articulate the risk properly enough.' "
Kawula, managing principal consultant at TriCon Elite Consulting, and O'Neill Sr., chief technologist at AWS Solutions, were sharing their expertise and wisdom gained from many years in the IT trenches in a recent half-day online event presented by Virtualization & Cloud Review titled "Hybrid Cloud Security Summit," which is now available for on-demand viewing.
C-Level Strategies
"So some of the strategies that I use when I'm working with the C-level teams, the boards of directors, is I don't just give them a summarization or my opinion," continued O'Neill Sr. "I bring in events from insurance -- our insurance broker or our auditors -- and I say, 'Hey, can you give me a few examples of other customers where their cybersecurity insurance didn't get renewed because of some event? Or can you give me an example of a audit that failed because proper levels of protection weren't put in place?'
"And I articulate those things to the CEOs and the boards of directors. Not in long-worded descriptions, but basically like, 'Hey, you know, if you look at this year, and our actual insurance broker says that they have processed claims for a billion dollars this year because of security events where malware has been involved.' And then I show them data where I say, 'Okay, of the 100 events ... about 15 percent of those companies never survived. They did not return back to business.' Okay. And when you describe those kinds of things, and you do it succinctly like that, you get that C-level support that says, 'No, we're going to do this.'
 "And then I show them data where I say, 'Okay, of the 100 events ... about 15 percent of those companies never survived. They did not return back to business.'"
"And then I show them data where I say, 'Okay, of the 100 events ... about 15 percent of those companies never survived. They did not return back to business.'"
John O'Neill Sr., chief technologist, AWS Solutions
"And in fact, Dave, you know this, I've been pretty successful at this where I get the C-level support that is actually needed to convince the lower level, the mid-management level. So the department heads, that kind of thing, who are like, 'No, you're not going to interrupt our production time, you're not going to interrupt our shipping schedules or whatever.' It's the C-level execs or the orders from the boards that come down and say, 'No, we are going to do this.' Or like you described earlier, where we talk about isolate, analyze and react -- selling that to the to the C suite is so critical in getting it to be able to change the modality and change the mental attitude of an organization at large."
Tough Conversations: 'You're Not the Best Friends of a Lot of Managers'
Kawula noted that IT security pros need to hold many other difficult conversations beyond the C suite as they seek to navigate today's ransomware- and malware-ridden cloudscapes.
 "The unfortunate reality is sometimes you need to make tough decisions. You need to lock out user accounts, you need to say, 'No, this is the third time you've now done this; you're going for retraining before your account is reactivated.'"
"The unfortunate reality is sometimes you need to make tough decisions. You need to lock out user accounts, you need to say, 'No, this is the third time you've now done this; you're going for retraining before your account is reactivated.'"
Dave Kawula, managing principal consultant, TriCon Elite Consulting
"Anybody that works in cybersecurity today, you know that you're not the best friends of a lot of managers inside of the organization," Kawula said. "Because the unfortunate reality is sometimes you need to make tough decisions. You need to lock out user accounts, you need to say, 'No, this is the third time you've now done this; you're going for retraining before your account is reactivated.' And if the users are not going to abide by the kind of rules of engagement, sometimes, you know, those users find other places of employment, right?"
More Conversations: The Good Kind
Continuing the communications theme, the duo noted that one positive conversation that can pay off is with your internet service provider, with whom it pays to establish a good relationship in advance of a cyberattack that, say, results in you needing to quickly repopulate your data. O'Neill Sr. noted that in such data transfer cases, speed is crucial.
"And that doesn't mean that you have to break the bank buying more WAN speed," he said. "If early on in the process, when you had to fail up to the cloud, if you get ahold of your provider, if you tell them what's going on, and you have an event and ask them to help partner with you and temporarily allow you to burst up or to increase your bandwidth, those kinds of conversations, they will often do that. And they'll do it at little to no charge because they want to have you as a long-term customer. And they know that this is a one-off event. And it's a real way for them to shine. Now, I will tell you that if you call into some national help desk where you're getting a level-1 help desk for, say, a national cable provider or something, you're probably not going to have much luck. So you need to kind of establish relationships with account executives at your connectivity providers well in advance of anything happening, so you know who to call, and when, and there'll be ready to act."
Kawula reiterated that advice in response to an audience member who asked for advice on negotiating with ISPs in the event of an emergency. "It's negotiate in advance," he replied. "Have those conversations in advance. Don't wait for the emergency, that you're trying to track somebody down. Have those negotiations in advance."
And the Insurance Companies
One last type of conversation a security pro might need to have is with insurance companies who are cracking down on cyber-attack policy rules and regulations, which can lead to a really awful experience.
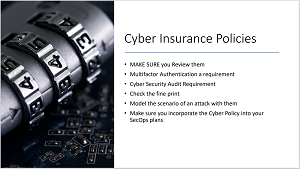 [Click on image for larger view.] A High-Level Cyber Insurance Polices Checklist
[Click on image for larger view.] A High-Level Cyber Insurance Polices Checklist
This problem was revisited in a discussion about testing backups.
"I want to point out that -- because a lot of people don't realize this -- that in this year 2022, we're starting to see a lot more activity in not just cyber insurance carrier requirements and external fiscal audit requirements, that kind of thing, but also in other areas," said O'Neill Sr., who noted that those other areas might be outside of the traditional security perimeter in today's hybrid cloud environments.
"And so they [insurance companies] want to not just verify that you have protections in place, but to verify that you can prove that those protections are in place and working. So you simply saying, 'Hey, I test my backups regularly,' isn't enough. They're gonna want screenshots, they're gonna want logs, they're gonna want results. And I often tell people that they're gonna want you to prove that you test each type of backup you take.
"So if you're backing up Exchange Online mailboxes, for instance, they want you to prove that you can restore a mailbox, they want you to prove that you can restore a file. If you're doing whole VHDX or VM backups, they want you to prove that you can restore and recover that entire server. And this is very important to the cyber insurance carriers, because the longer it takes you to get back up and running, after an event, a malware event, ransomware event ... the longer it takes you, the more it costs you and the more it costs them as the insurance carrier -- their potential exposure.
"So they're going to start coming at you harder than ever this year and next year and beyond. To prove that you have tested all of your backups regularly, so probably more than once a year, probably even more than twice a year, and that you're testing each type of backup you take. So if you're doing SQL database backups, you need to prove that you can do a SQL database restore."
Automation, Immutability and More
One approach that might help with that is PowerShell automation, replied Kawula, who along with O'Neill Sr. detailed many other specific cybersecurity strategies for the online audience of hundreds. Along with testing backups, they discussed immutability, offsite/dark copies of data, failing over to the cloud, cyber business continuity planning, advanced persistent threat protection, vulnerability assessments, training, unsupported hardware, Zero Trust, Multi-Factor Authentication (MFA) and much more.
While their presentation -- one of three in the half-day summit -- is available for on-demand viewing, IT pros who attend such events live can interact with experts in Q&A sessions (and even win a drawing for a big prize). With that in mind, here are some summits coming up in the next month:
The full list of future and on-demand summits can be found here.