
Red Hat Summit 2026 announcements around Telenet Business and NASA's Jet Propulsion Laboratory show OpenShift Virtualization being positioned as a platform for VM modernization, hybrid cloud operations and future containerized workloads.

Tom Fenton examines the diverse thin-client marketplace beyond recent consolidation, revealing that major hardware vendors have commoditized their devices and under-invested in proprietary operating systems, creating opportunities for third-party software platforms like IGEL, 10ZiG, and Citrix eLux to dominate the software-defined endpoint space.

After finding his recent presentation well received, Tom Fenton puts it online.

Tom Fenton tests MacStadium's remote macOS desktops and finds a smooth, high-performance experience -- despite Apple's virtualization hurdles.

Enhanced integration allows customers to secure and protect data from virtual machines (VMs) and containers within their Red Hat OpenShift environments using Cohesity DataProtect and NetBackup.

With his home network a mess, Tom Fenton explores how to bring some sense of order using readily available, easy-to-use, free tools.
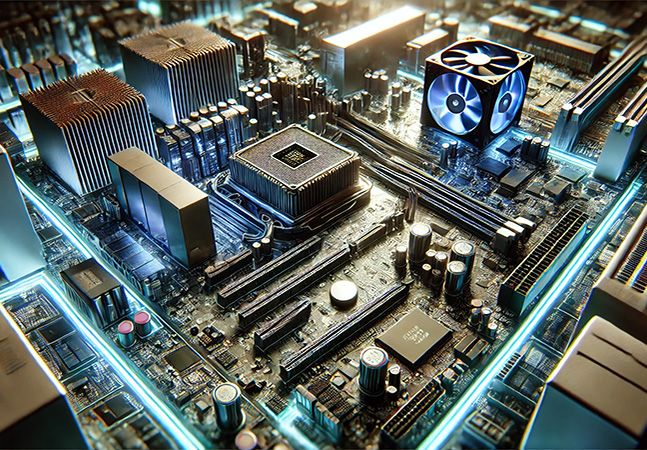
In part three of his series, Tom Fenton configures ESXi to use an NTP server for precise time synchronization, enables SSH access, and adds a datastore for storing and running virtual machines.
Post-acquisition defections have been trumpeted by benefactors, with the latest being Nutanix announcing that Evalueserve, a global research and analytics firm, has chosen Nutanix to replace its VMware-based virtualization infrastructure.

It just became free for commercial use along with earlier permission for personal use, so Tom Fenton shares some of the cool things you can do with this venerable virtualization platform.

Nutanix announced a new hybrid cloud offering parked on AWS that can help users extend their on-premises Nutanix environments to the cloud, offering perks to other users possibly disgruntled by the ongoing Broadcom/VMware tumult.

Research firm Gartner predicts an enterprise trend "to replace their VMware-based deployments and embrace hybrid cloud infrastructure delivery," with Nutanix often chosen as the alternative.

Tom explains how things shook out and what it means to you after VMware's End User Computing (EUC) division emerged as an independent entity, now operating under the name Omnissa.

Here's an in-depth examination of many new features and enhancements.

This release of vSAN focuses on three significant areas: flexible topologies, agile data protection and enhanced management.

Broadcom's latest update to its VMware Cloud Foundation (VCF) private cloud offering is aimed at boosting infrastructure modernization, increasing developer productivity and enhancing security/resiliency.