
Tom Fenton explains how this is huge news for the tens of thousands of students, hobbyists and casual users who would like to run multiple instances of OSes on a single computer.

Microsoft extended its small language model (SLM) technology along with cloud-based large language models (LLMs) to the device level with the introduction of Copilot+ PCs, which leverage powerful processors and multiple state-of-the-art AI models.

As expected, the kickoff of Google I/O 2024 was heavy on the AI, with new updates for the company's cloud-based Vertex AI service leading a slew of day 1 announcements centered around generative AI.

Tom recaps an end-user computing conference heavy on the tech (no sales) featuring "choose your own adventure" and what to pack for bug-out bags for tech emergencies.

IBM is jumping on the Copilot AI assistant bandwagon popularized by Microsoft with a new IBM Copilot Runway initiative.
OpenAI is working on a Model Spec document that specifies desired behavior for its models in its API and ChatGPT.
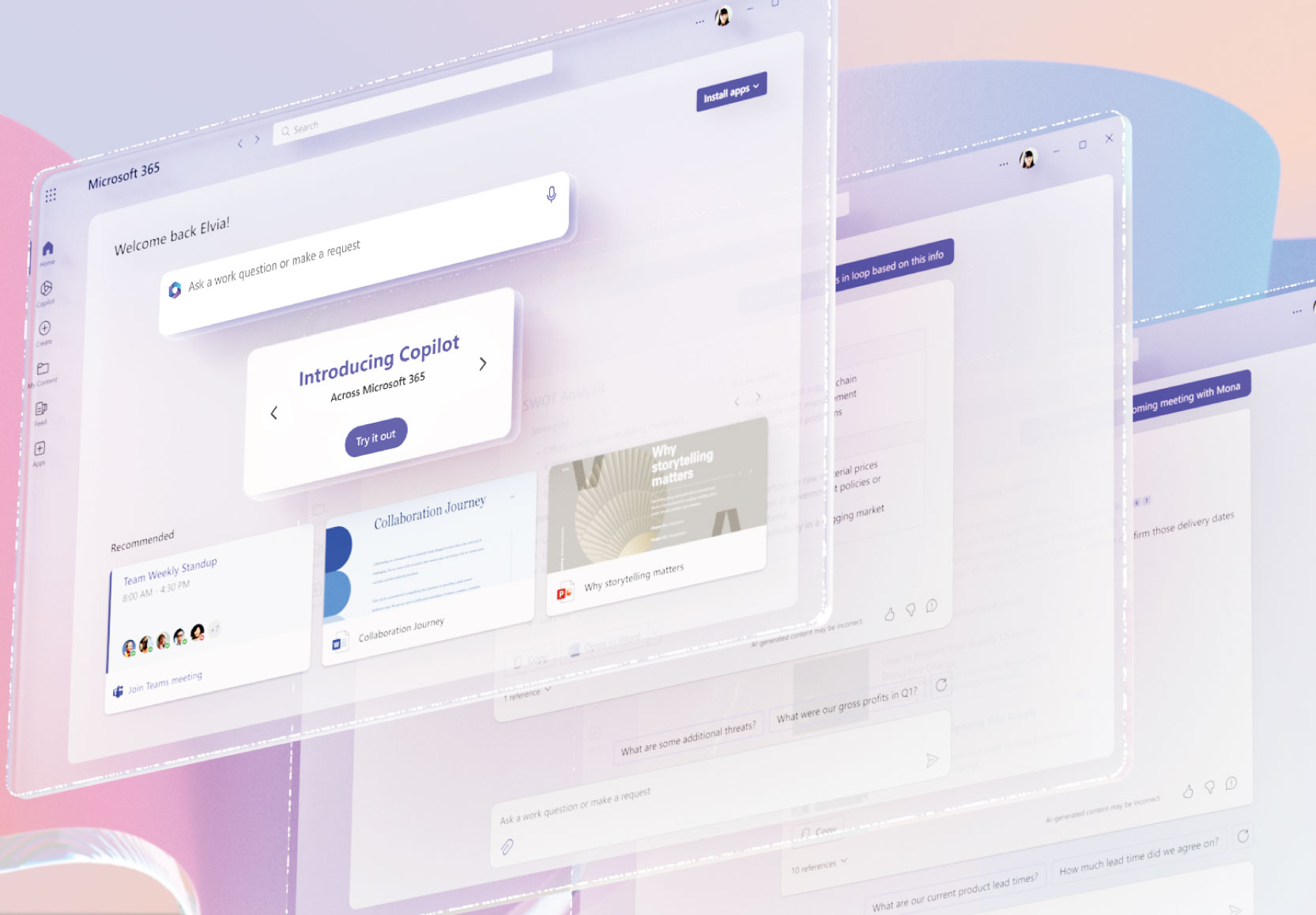
In announcing its fourth annual Work Trend Index report yesterday, Microsoft teased AI features coming up for Microsoft 365, its cloud-based productivity suite.

Microsoft published a 2024 Work Trend Index delving into the "state of AI at work," finding that many employees are increasingly hungry for AI tools and won't wait for their employers to provide them.

New Gartner research on providers of cloud AI developer services shows the usual cast of characters leading the pack.

During this week's RSA Conference, the CSA announced new guidance for organizations to successfully implement AI, with recommendations focusing on security and compliance.

"We are acting quickly to correct this misinformation because, as Winston Churchill correctly said, 'A lie gets halfway around the world before the truth has a chance to get its pants on.' "

Frustrated by outdated info? Here's a roundup of the knowledge cutoff dates and internet search abilities of some top freely available online AI sites.

Brien Posey explains how to use the AWS Tools for PowerShell to make AWS services accessible through the PowerShell interface, providing extra capabilities.

Earlier predictions of a decline in ransomware attacks have not borne out and organizations in the healthcare sector -- where sensitive data abounds -- are being hit particularly hard, according to a new report from Zero Trust data security specialist Rubrik.

Many more new features than last release, explained in detail by Paul Schnackenburg: "Maybe Microsoft has realized that not everything is in the cloud, and giving attention to Server is important."
- By Paul Schnackenburg
- 04/30/2024

Two new survey-based reports from a cloud giant and a research firm each list trends for Data and AI/analytics in 2024, finding some commonalities such as the democratization of AI, the need for data literacy and more.
So what is possible with small language models, and when should an organization go big or small?

In Meta's recent quarterly earnings reports, CEO Mark Zuckerberg addressed the company's huge investments into the technologies while only mentioning the metaverse in the context of AI. Meta.ai answers your questions about what's going on.

Cloud giants continue to up their AI games, with brand-new developments including a tiny language model suitable for a phone from Microsoft, while Amazon's Bedrock AI service now sports Meta's Llama 3 models and much more.

Broadcom is still dealing with widespread backlash over changes -- many affecting licensing -- made to VMware products after its acquisition of that company, but some critics and users met recent announcements with skepticism and derision.