In-Depth
Expert Consultant Details How to Secure the Machine Identity Attack Surface
Sergey Chubarov believes that as organizations add more automation, service integrations and software-driven workflows, security teams need to pay closer attention to the identities that are not tied to individual people. Service accounts, API keys and tokens rarely generate the same day-to-day scrutiny as user accounts, but they can quietly accumulate permissions, persist long after their original purpose has faded and become attractive targets for attackers.
 "Without proper governance, then we will just have explosion of non human identities, NHI with lots of permissions."
"Without proper governance, then we will just have explosion of non human identities, NHI with lots of permissions."
Sergey Chubarov, Consultant, Instructor and Conference Speaker
He shared those insights during his session today at the Identity at the Edge: Securing Access in the Age of AI online tech-education summit, which was presented by RedmondMag and is being made available for on-demand replay by Okta. Sergey's presentation, "Securing Non-Human Identity: Bots, APIs, and Autonomous Agents in the AI Era," concentrated less on AI agents themselves and more on the broader class of non-human identities already embedded across enterprise environments.
Sergey is a consultant, instructor and conference speaker whose bio lists Microsoft MVP: Cloud Security along with multiple offensive-security and training credentials. He opened by defining non-human identities as the identities that let applications, services and automation tools access systems and data independently. In his framing, that category includes service accounts, API keys, tokens and similar machine-facing credentials, while AI agents add an additional layer of complexity on top of that already sprawling identity surface.
 [Click on image for larger view.] Non-human Identities and AI agents (source: Sergey Chubarov).
[Click on image for larger view.] Non-human Identities and AI agents (source: Sergey Chubarov).
He said the central problem is governance. When these identities are created in large numbers without consistent review, ownership or lifecycle controls, they can remain in the environment with broad permissions and little visibility. The slide deck summarized that point directly, warning that without proper governance non-human identities can accumulate excessive permissions or remain unnoticed, increasing security exposure. Sergey also noted in the session that organizations may already be treating AI agents as a separate category, but the more immediate challenge for many shops is the sheer number of non-human identities already in use.
From there, he moved into the operational challenge: machine identities are harder to oversee than human ones because there is no individual user behind them to report suspicious behavior or to naturally trigger governance processes. His slides described non-human identities as frequently unmanaged, often highly privileged and a significant attack vector, while also citing an estimate that they outnumber human identities by 80 to 1. That combination of scale and weak visibility, he said, makes monitoring and remediation far more difficult than for ordinary user accounts.
 [Click on image for larger view.] NHI Challenges (source: Sergey Chubarov).
[Click on image for larger view.] NHI Challenges (source: Sergey Chubarov).
Sergey used that setup to explain why the problem keeps getting worse in practice. One of the clearest examples came in his discussion of hardcoded secrets, where he pointed to GitGuardian data showing 28.65 million new hardcoded secrets in public GitHub commits in 2025. He used that statistic not as a throwaway number, but as evidence that credentials are still routinely being left in places they should never be, including source code and other developer-accessible locations. His point was that non-human identity risk is not limited to abstract governance theory; it often starts with something as basic as a secret being exposed and left usable.
 [Click on image for larger view.] 28.65 Million New Hardcoded Secrets in Public GitHub Commits (source: Sergey Chubarov).
[Click on image for larger view.] 28.65 Million New Hardcoded Secrets in Public GitHub Commits (source: Sergey Chubarov).
That helped connect the earlier governance discussion to a more concrete security reality. Service accounts, API keys and tokens may be invisible to most users, but they are not invisible to attackers. Sergey said credentials tied to non-human identities can sit unchanged for years, and once they are exposed, organizations may not even realize how many applications or services depend on them. That makes cleanup harder, and it helps explain why compromised machine credentials can become the starting point for much larger incidents.
He also tied that risk to real-world breach activity, citing examples of attackers exploiting compromised API keys and exposed cloud credentials to move laterally through environments. The broader takeaway was that non-human identities can offer attackers a quieter entry point than human accounts because they often carry significant privileges without attracting the same oversight or authentication controls.
After outlining the risks, Sergey shifted into what security teams should actually do. He said the first step is posture management: discovering and labeling non-human identities, finding stale or unused accounts and surfacing issues such as unrotated passwords, unused tokens and service accounts that no longer appear necessary. Instead of treating machine identities as background plumbing, he argued that organizations need a clearer inventory and clearer accountability around them.
 [Click on image for larger view.] Posture Management (source: Sergey Chubarov).
[Click on image for larger view.] Posture Management (source: Sergey Chubarov).
That advice tied back to one of the session's broader themes: the problem is often less about any single secret or service account than about the inability to see the whole environment clearly. If organizations do not know which non-human identities exist, what they access and whether they are still required, they are left making security decisions in the dark. Sergey presented discovery and labeling as foundational work that has to happen before tighter controls can be applied consistently.
He then moved into the live-demo portion of the talk, showing how those concepts surface in actual tools. The most useful demo for article purposes was his look at Okta's non-human identity dashboard, which illustrated the scale problem visually by surfacing service accounts, access keys, API tokens and issue categories in one place. He used that screen to show how teams can spot problems such as unused accounts, old passwords and credentials that have not been rotated, rather than trying to piece that information together manually across disconnected systems.
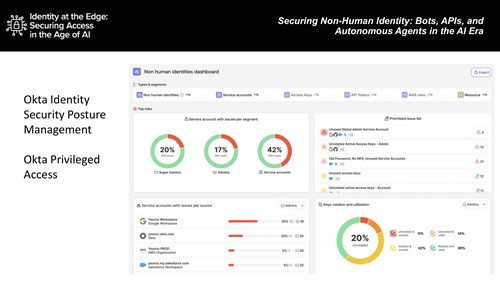 [Click on image for larger view.] Okta Identity Security Posture Management and Okta Privileged Access (source: Sergey Chubarov).
[Click on image for larger view.] Okta Identity Security Posture Management and Okta Privileged Access (source: Sergey Chubarov).
That demo section also reinforced one of Sergey's recurring points: managing non-human identities manually becomes unrealistic once the environment grows large enough. Replay viewers will be able to see that more clearly in the full session, where he walked through the actual dashboards and controls. In article form, the key takeaway is that the tools are increasingly built to treat machine identities as a first-class identity-security problem, not just an application-side detail for developers to worry about.
Across the session, Sergey's message was that service accounts, API keys and similar credentials deserve the same kind of sustained governance attention that organizations already give to human identities. His presentation moved from defining the problem, to showing how exposed secrets and unmanaged credentials create risk, to explaining that the fix starts with visibility: know what machine identities exist, know what they can do and know when they have become a liability rather than a necessity.
And More
And, although replays are fine -- this was just today, after all, so timeliness isn't an issue -- there are benefits of attending such summits and webcasts from Virtualization & Cloud Review and sister sites in person. Paramount among these is the ability to ask questions of the presenters, a rare chance to get one-on-one advice from bona fide subject matter experts (not to mention the chance to win a free prize, in this case Bose Noise-Cancelling Headphones thanks to Okta, which also presented at the summit). With all that in mind, here are some upcoming summits and webcasts coming up: