
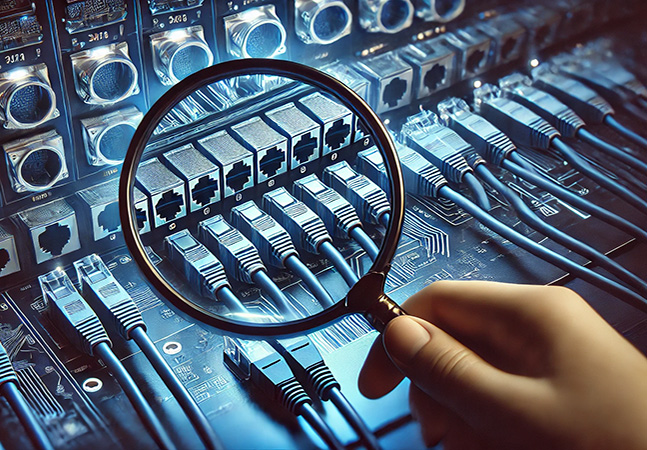
In his final article of a series, Tom Fenton shows how he used ntopng Community edition dashboards to analyze his local LAN network traffic.

In today's rapidly evolving cybersecurity landscape, IT infrastructure is under constant siege from increasingly sophisticated threats. Ransomware, insider attacks, and supply chain vulnerabilities have escalated in both frequency and impact, leaving organizations scrambling to fortify their defenses. At the same time, the shift to hybrid work, cloud adoption, and AI-driven threats can make some traditional security models obsolete, demanding a more proactive and adaptive approach.
In the third part of a series, Tom Fenton explains how he set up and installed ntopng, along with detailing where it will sit in his home/lab network and how he redirected traffic to it.

One interesting trend in a new report from Wiz about AI in the cloud is the disruption caused by the arrival of a DeepSeek model that caused an uptick in self-hosted models, industry backlash and usage restrictions.
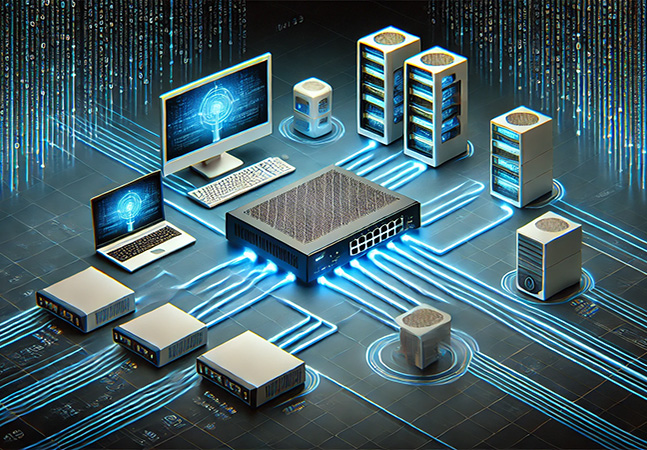
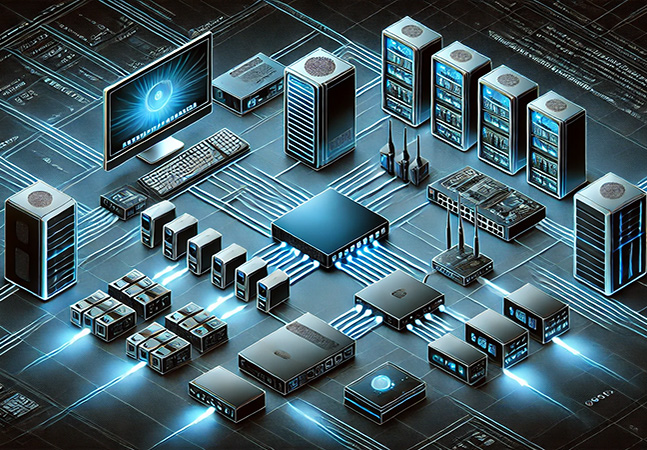
Tom Fenton gets geeky in detailing how he is using ntopng to monitor and visualize network traffic in his home LAN, which he embarrassingly lost control of.

In an accidental termination, thankfully, there are a few things that you can do to protect yourself against the loss of a critical instance, Brien Posey explains.

With cybersecurity affecting everyone, a multicloud environment might be of special concern because of all the moving parts and associated system and their connections, possibly introducing new attack vectors or specialized attack strategies, so front-line expert Chris Spinks provides action-item best practices.

Paul Schnackenburg looks at Microsoft's entry in the Secure Services Edge (SSE) market, Global Secure Access (GSA), and the different flavors of it, Internet Access and Private Access. Another buzzword for this kind of technology is Zero Trust Network Access, ZTNA.
- By Paul Schnackenburg
- 02/26/2025
With his home network a mess, Tom Fenton explores how to bring some sense of order using readily available, easy-to-use, free tools.

"Don't think your company's too small to be cyberattacked, because you're not," says disaster recovery expert Joey D'Antoni. "It just means they haven't decided to try you yet."

Veeam Software, a data resilience specialist, announced the enhancement of its disaster recovery capabilities for Microsoft Hyper-V environments through the introduction of orchestration features.

Tom Fenton waited 23 years for Linux software installation CLI functionality to come to Windows.

After Microsoft seized on its OpenAI partnership to establish a solid leadership position in the cloud AI space, and Google quickly declared a "code red" emergency to catch up with first Bard and then Gemini, Amazon wasn't making as much news in AI. That has changed.
Concluding his series, Tom Fenton provides step-by-step instructions for creating a VM from different Linux distributions and discusses issues with running Windows on it.

Threat actors are changing tactics as they collect less money from ransomware payoffs, according to a new report from Chainalysis, a blockchain analytics firm.

Google opened up access to Gemini 2.0, a significant update to its flagship AI, targeting enterprise users and developers with enhanced multimodal capabilities and improved performance.
GenAI dominates the new Nutanix Cloud Index, the latest in a years-long series of surveys the hybrid multicloud specialist publishes to measure global enterprise progress with cloud adoption. The 2025 report published today reveals that GenAI is changing organizations' priorities, with security and privacy being a primary concern.

In part three of his series, Tom Fenton configures ESXi to use an NTP server for precise time synchronization, enables SSH access, and adds a datastore for storing and running virtual machines.

The Cloud Security Alliance has weighed in on the debut of revolutionary and controversial DeepSeek AI with strategic implications and action items just as a report was published on data leakage from the platform.
Tom Fenton walks through the process of installing and using ESXi 8 on the Raspberry Pi 5, providing a hands-on opportunity to explore VMware virtualization technology or to run ARM-based VMs.