-

By Tom Fenton
KubeCon 2026 EU's second day explored how enterprises can balance digital sovereignty with open-source collaboration -- with speakers arguing that organizations must distinguish between a unified global codebase and locally controlled operational deployments -- while showcasing real-world Kubernetes applications ranging from France's national railway infrastructure to satellite-based environmental monitoring.
-

By Tom Fenton
KubeCon EU 2026 drew a record 13,500 attendees to Amsterdam -- the largest open-source software meetup in history. Day 1 keynotes centered on AI infrastructure: NVIDIA joined CNCF as a Platinum member and donated its GPU driver as a standard reference for the Kubernetes DRA API, while new projects like AICR and LLM-D tackle the distributed inference challenge at scale. Virtualization & Cloud Review's Tom Fenton reports from the show floor.
-

The designation was based on end-user feedback for backup and data protection platforms.
-
Stephen L. Rose's TechMentor session offers IT pros a practical, beginner-friendly path into Copilot automation, including agents, prompts, connectors, actions and the governance controls needed to manage them securely.
-

Our 1-person SOC from Down Under explains how, as enterprise organizations outside the U.S. increasingly seek alternatives to American public cloud providers, Microsoft is responding with a spectrum of sovereign cloud options -- from country-specific Azure regions and national partner clouds to fully disconnected on-premises clusters running Azure Linux.
-

By Tom Fenton
Tom Fenton's on-the-ground report from KubeCon Europe 2026 in Amsterdam reveals that enterprises are actively pursuing Kubernetes-based alternatives to legacy VM infrastructure -- with a pre-conference "VM on Kubernetes Day" event and vendor discussions with Cast AI and ZEDEDA highlighting real-world strategies for migration, cloud cost optimization, and edge AI deployment.
-
By Tom Fenton
Running an LLM on a Raspberry Pi with Ollama is easy to set up in minutes, but practical performance depends heavily on choosing a smaller model tuned for low-power hardware.
-
By Tom Fenton
This first article in a series explains the core AI concepts behind running LLM and RAG workloads on a Raspberry Pi, including why local AI is useful and what tradeoffs to expect.
-

By Tom Fenton
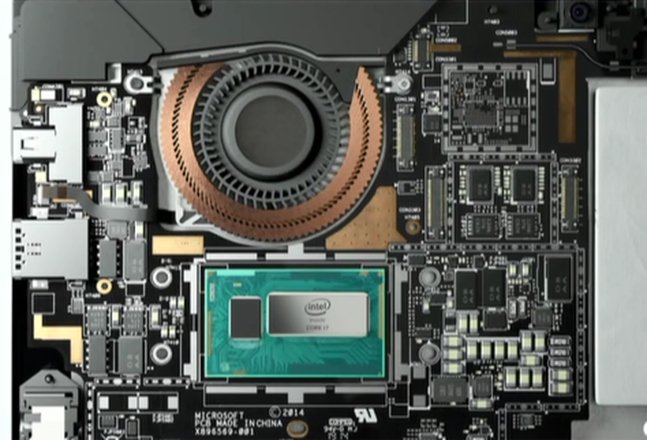
Tom Fenton's benchmark data across the Pi 400, Pi 500, Pi 500+, and Pi 5 shows the Pi 500+ delivering the strongest all-around desktop performance with notable gains in CPU, graphics, and networking.
-

A hands-on PoC with Microsoft Copilot Studio found that creating a basic agent was easy, but getting useful results from a SharePoint-hosted Excel tracker required extra connection setup and worked better only after separate worksheet tabs were split into distinct files.
-
New agentic AI offering targets release-note review, impact analysis and test planning for enterprise SaaS updates.
-
By Tom Fenton
The Raspberry Pi 500+ upgrades the computer-in-a-keyboard concept with 16GB of RAM, a 256GB NVMe SSD, and a mechanical keyboard -- all built on the same Broadcom BCM2712 processor as the Pi 5 and Pi 500.
-

Rubrik and Microsoft announced an integration at RSAC 2026 connecting Defender's identity threat detection with Rubrik's automated rollback and recovery, covering Active Directory and Entra ID in hybrid cloud environments.
-

AWS and Google Cloud used GTC 2026 to detail new NVIDIA-based cloud offerings spanning GPU scale-out, inference, orchestration, and flexible consumption models, while related NVIDIA announcements added context for the company's broader AI cloud strategy.
-

Rubrik announced Rubrik Data Protection for Google Workspace, positioning it as a unified cyber-resilience offering for Gmail and Google Drive with recovery, policy and continuity features.
-

By Tom Fenton
Enterprises face five hard truths when scaling AI from successful pilots to production -- governance gaps, AI agent sprawl, security as an afterthought, agent unpredictability, and the absence of shared architecture -- all lessons that mirror the chaotic early days of API development and demand the same solutions that eventually tamed it.
-

By Tom Fenton
Edera's Micro VM platform isolates each Kubernetes pod in its own private Linux kernel using a Rust-based, Xen-derived hypervisor -- reducing the container attack surface by up to 95% while maintaining near-native performance
-

By Tom Fenton
After splitting from VMware in 2024, Omnissa Horizon has evolved with expanded platform support including Nutanix AHV, modernized client interfaces, AI-powered tools, and flexible hybrid cloud deployment options while maintaining its enterprise VDI foundation.
-

Security expert Brien Posey outlined why the data layer is a prime target and shared practical protection principles: know what you have, limit access, encrypt data and use strong authentication.
-
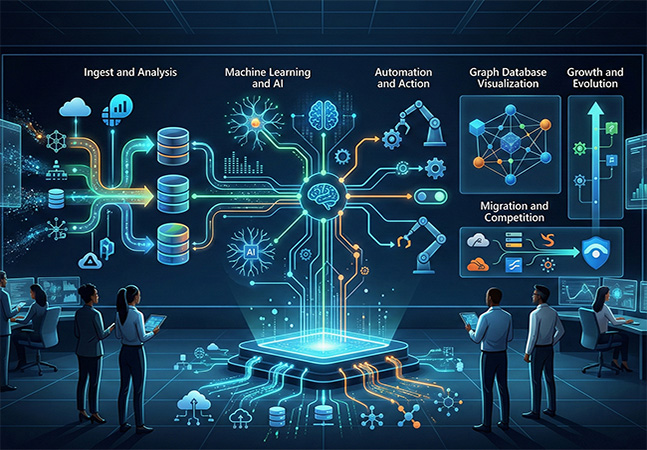
Our 1-person SOC from Down Under explains how Microsoft Sentinel has rapidly evolved from its 2019 launch to become a leading cloud-based SIEM solution, now featuring advanced capabilities like graph databases, AI agents, data lake storage, and seamless XDR integration.
-

By Tom Fenton
A Q&A recap from a December 4th, 2025 webinar covers key Kubernetes and cloud-native trends from KubeCon '25, including AI operations, security, observability, and enterprise adoption.
-

By Tom Fenton
Tom Fenton explains why he's attending KubeCon Europe 2026 in Amsterdam despite having just attended the North America conference, highlighting the unique Euro-centric themes, networking opportunities with European maintainers, fresh AI-focused content, and the event's convenient logistics and comprehensive schedule.
-
By Tom Fenton
In Tom Fenton's conversation with Solo.io Global Field CTO Christian Posta, the discussion focused on operationalizing AI agents and skills as production-grade, governed resources--including how kagent and agentgateway fit into scaling agent deployments securely across enterprise environments.
-

Veeam unveiled Agent Commander, a unified platform designed to detect AI risk, protect AI systems and precisely undo AI-driven actions at enterprise scale.
-
Druva introduced Deep Analysis Agents, Agentic Memory and multimodal capabilities to move DruAI from conversational assistance to delegated investigative workflows.